More on Personal Growth

Entreprogrammer
3 years ago
The Steve Jobs Formula: A Guide to Everything
A must-read for everyone
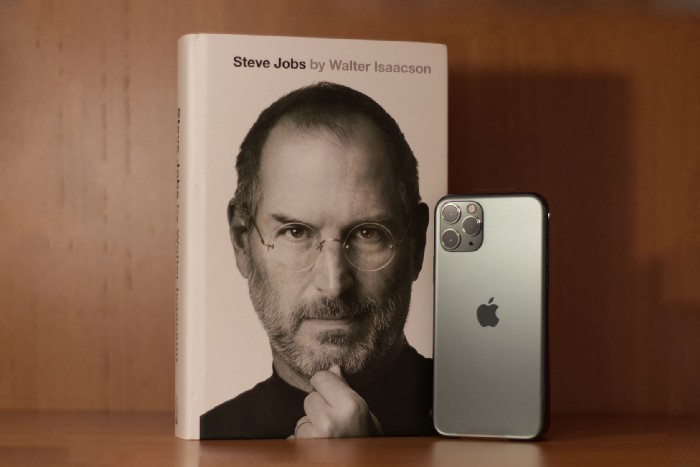
Jobs is well-known. You probably know the tall, thin guy who wore the same clothing every day. His influence is unavoidable. In fewer than 40 years, Jobs' innovations have impacted computers, movies, cellphones, music, and communication.
Steve Jobs may be more imaginative than the typical person, but if we can use some of his ingenuity, ambition, and good traits, we'll be successful. This essay explains how to follow his guidance and success secrets.
1. Repetition is necessary for success.
Be patient and diligent to master something. Practice makes perfect. This is why older workers are often more skilled.
When should you repeat a task? When you're confident and excited to share your product. It's when to stop tweaking and repeating.
Jobs stated he'd make the crowd sh** their pants with an iChat demo.
Use this in your daily life.
Start with the end in mind. You can put it in writing and be as detailed as you like with your plan's schedule and metrics. For instance, you have a goal of selling three coffee makers in a week.
Break it down, break the goal down into particular tasks you must complete, and then repeat those tasks. To sell your coffee maker, you might need to make 50 phone calls.
Be mindful of the amount of work necessary to produce the desired results. Continue doing this until you are happy with your product.
2. Acquire the ability to add and subtract.
How did Picasso invent cubism? Pablo Picasso was influenced by stylised, non-naturalistic African masks that depict a human figure.
Artists create. Constantly seeking inspiration. They think creatively about random objects. Jobs said creativity is linking things. Creative people feel terrible when asked how they achieved something unique because they didn't do it all. They saw innovation. They had mastered connecting and synthesizing experiences.
Use this in your daily life.
On your phone, there is a note-taking app. Ideas for what you desire to learn should be written down. It may be learning a new language, calligraphy, or anything else that inspires or intrigues you.
Note any ideas you have, quotations, or any information that strikes you as important.
Spend time with smart individuals, that is the most important thing. Jim Rohn, a well-known motivational speaker, has observed that we are the average of the five people with whom we spend the most time.
Learning alone won't get you very far. You need to put what you've learnt into practice. If you don't use your knowledge and skills, they are useless.
3. Develop the ability to refuse.
Steve Jobs deleted thousands of items when he created Apple's design ethic. Saying no to distractions meant upsetting customers and partners.
John Sculley, the former CEO of Apple, said something like this. According to Sculley, Steve’s methodology differs from others as he always believed that the most critical decisions are things you choose not to do.
Use this in your daily life.
Never be afraid to say "no," "I won't," or "I don't want to." Keep it simple. This method works well in some situations.
Give a different option. For instance, X might be interested even if I won't be able to achieve it.
Control your top priority. Before saying yes to anything, make sure your work schedule and priority list are up to date.
4. Follow your passion
“Follow your passion” is the worst advice people can give you. Steve Jobs didn't start Apple because he suddenly loved computers. He wanted to help others attain their maximum potential.
Great things take a lot of work, so quitting makes sense if you're not passionate. Jobs learned from history that successful people were passionate about their work and persisted through challenges.
Use this in your daily life.
Stay away from your passion. Allow it to develop daily. Keep working at your 9-5-hour job while carefully gauging your level of desire and endurance. Less risk exists.
The truth is that if you decide to work on a project by yourself rather than in a group, it will take you years to complete it instead of a week. Instead, network with others who have interests in common.
Prepare a fallback strategy in case things go wrong.
Success, this small two-syllable word eventually gives your life meaning, a perspective. What is success? For most, it's achieving their ambitions. However, there's a catch. Successful people aren't always happy.
Furthermore, where do people’s goals and achievements end? It’s a never-ending process. Success is a journey, not a destination. We wish you not to lose your way on this journey.

Neeramitra Reddy
3 years ago
The best life advice I've ever heard could very well come from 50 Cent.
He built a $40M hip-hop empire from street drug dealing.

50 Cent was nearly killed by 9mm bullets.
Before 50 Cent, Curtis Jackson sold drugs.
He sold coke to worried addicts after being orphaned at 8.
Pursuing police. Murderous hustlers and gangs. Unwitting informers.
Despite his hard life, his hip-hop career was a success.
An assassination attempt ended his career at the start.
What sane producer would want to deal with a man entrenched in crime?
Most would have drowned in self-pity and drank themselves to death.
But 50 Cent isn't most people. Life on the streets had given him fearlessness.
“Having a brush with death, or being reminded in a dramatic way of the shortness of our lives, can have a positive, therapeutic effect. So it is best to make every moment count, to have a sense of urgency about life.” ― 50 Cent, The 50th Law
50 released a series of mixtapes that caught Eminem's attention and earned him a $50 million deal!
50 Cents turned death into life.
Things happen; that is life.
We want problems solved.
Every human has problems, whether it's Jeff Bezos swimming in his billions, Obama in his comfortable retirement home, or Dan Bilzerian with his hired bikini models.
All problems.
Problems churn through life. solve one, another appears.
It's harsh. Life's unfair. We can face reality or run from it.
The latter will worsen your issues.
“The firmer your grasp on reality, the more power you will have to alter it for your purposes.” — 50 Cent, The 50th Law
In a fantasy-obsessed world, 50 Cent loves reality.
Wish for better problem-solving skills rather than problem-free living.
Don't wish, work.
We All Have the True Power of Alchemy
Humans are arrogant enough to think the universe cares about them.
That things happen as if the universe notices our nanosecond existences.
Things simply happen. Period.
By changing our perspective, we can turn good things bad.
The alchemists' search for the philosopher's stone may have symbolized the ability to turn our lead-like perceptions into gold.
Negativity bias tints our perceptions.
Normal sparring broke your elbow? Rest and rethink your training. Fired? You can improve your skills and get a better job.
Consider Curtis if he had fallen into despair.
The legend we call 50 Cent wouldn’t have existed.
The Best Lesson in Life Ever?
Neither avoid nor fear your reality.
That simple sentence contains every self-help tip and life lesson on Earth.
When reality is all there is, why fear it? avoidance?
Or worse, fleeing?
To accept reality, we must eliminate the words should be, could be, wish it were, and hope it will be.
It is. Period.
Only by accepting reality's chaos can you shape your life.
“Behind me is infinite power. Before me is endless possibility, around me is boundless opportunity. My strength is mental, physical and spiritual.” — 50 Cent

Andy Murphy
3 years ago
Activating Your Vagus Nerve
11 science-backed ways to improve health, happiness, healing, relaxation, and mental clarity.

Vagus nerve is the main parasympathetic nervous system component.
It helps us rest and digest by slowing and stabilizing a resting heart rate, slowing and stabilizing the breath, promoting digestion, improving recovery and healing times, producing saliva, releasing endorphins and hormones like dopamine, oxytocin, and serotonin, and boosting the immune, digestive, and cardiovascular systems.
The vagus nerve sends anti-inflammatory signals to other parts of the body and is located behind the tongue, in the throat, neck, heart, lungs, abdomen, and brainstem.
Vagus means wandering in Latin. So, it's bold.
Here are 11 proven ways to boost health, happiness, and the vagus nerve.
1. Extend
“Yoga stimulates different nerves in your body, especially the vagus nerve that carries information from the brain to most of the body’s major organs, slows everything down and allows self-regulation. It’s the nerve that is associated with the parasympathetic system and emotions like love, joy, and compassion.” — Deepak Chopra
Stretching doesn't require a yoga background.
Listen to your body and ease into simple poses. This connects the mind and body.
If you're new to yoga or don't have access to an in-person class, try Yoga with Adrienne. Over 600 YouTube videos give her plenty of material.
2. Inhale
Because inhaling and exhaling activate the autonomic nervous system, we can breathe to relax.
Exhaling activates the parasympathetic nervous system (rest and digest). One inhales stress, the other exhales it.
So, faster or more intense breathing increases stress. Slower breathing relaxes us.
Breathe slowly, smoothly, and less.
Rhythmic breathing helps me relax.
What to do is as follows:
1. Take 4 smooth, forceless nose breaths.
2. Exhale smoothly and forcefully for 4 seconds
3. Don't pause at the inhale or exhale.
4. Continue for 5 minutes/40 breaths
5. Hold your breath as long as comfortable.
6. Breathe normally.
If four seconds is too long, try breathing in and out for two seconds, or in and out for three seconds, until your breath naturally relaxes. Once calmer, extend your breath.
Any consistent rhythm without force is good. Your heart will follow your lead and become coherent.
3. Chant/Hum
Singing, chanting, or humming activate the vagus nerve through the back of the throat.
Humming emits nitric oxide.
Nitric oxide improves blood circulation, blood flow, heart health, and blood pressure.
Antiviral, antibacterial, anti-inflammatory, antioxidant, and antimicrobial properties kill viruses and bacteria in the nose and throat.
Gargling water stimulates the vagus nerve.
Simple ways to heal, boost energy, and boost mood are often the healthiest. They're free and can be done anywhere.
4. Have more fun
Laughing stimulates the throat muscles, activating the vagus nerve. What's not to like? It releases dopamine.
Take time to enjoy life. Maybe it's a book, podcast, movie, socializing with friends, or laughing yoga.
Follow your bliss, as Joseph Campbell says.
Laugh at yourself
Actually. Really.
Gagging activates vagus nerve-connected muscles. Some doctors use the gag reflex to test the vagus nerve.
Grossness isn't required. While brushing, gag quickly. My girlfriend's brother always does it.
I'm done brushing when I gag, he says.
6. Take in the outdoors
Nature relaxes body and mind. Better if you can walk barefoot.
Earthing is associated with hippies dancing in daisies.
Science now supports hippies.
7. Enter some chilly water.
The diving reflex activates the vagus nerve when exposed to cold water.
The diving reflex involves holding your breath in cold water. Cold showers work best.
Within minutes of being in cold water, parasympathetic nervous system activity, which calms the body, increases.
8. Workout
Exercise increases dopamine, blood circulation, and breathing. So we feel energized, calm, and well-rested.
After resting, the parasympathetic nervous system engages.
It's worth waiting for, though.
9. Play music with brainwaves
Brainwave music harmonizes brainwave activity, boosts productivity and mental clarity, and promotes peace and relaxation by stimulating the vagus nerve.
Simply play a song.
My favorite.
10. Make gentle eyes
Eyes, like breath, often reflect inner state. Sharp, dilated, focused eyes indicate alertness.
Soft, open eyes reflect relaxation and ease. Soft eyes relax the nervous system.
This practice reduces stress, anxiety, and body tension. It's a quick and effective way to enter a calm, peaceful state.
Wild animals can be hunted one minute and graze the next.
Put it into action:
Relax while seated.
Gaze at a distant object
Use peripheral vision while looking straight ahead
Without moving your eyes, look up and down. Connect side spaces to your vision.
Focus on everything as your eyes soften.
Keep breathing
Stay as long as you like
11. Be intimate
We kiss, moan, and breathe deeper during love. We get dopamine, oxytocin, serotonin, and vagus nerve stimulation.
Why not?
To sum up
Here are 11 vagus nerve resets:
Stretch
Breathe
Hum/Chant
More humor
Amuse yourself
Spend time outdoors
Leap into chilly water
Exercise
Play music with brainwaves.
Make gentle eyes.
Be intimate
If these words have inspired you, try my favorite breathwork technique. Combining breathing, chanting, and brainwave music. Win-win-win :)
You might also like

Antonio Neto
3 years ago
What's up with tech?
Massive Layoffs, record low VC investment, debate over crash... why is it happening and what’s the endgame?

This article generalizes a diverse industry. For objectivity, specific tech company challenges like growing competition within named segments won't be considered. Please comment on the posts.
According to Layoffs.fyi, nearly 120.000 people have been fired from startups since March 2020. More than 700 startups have fired 1% to 100% of their workforce. "The tech market is crashing"
Venture capital investment dropped 19% QoQ in the first four months of 2022, a 2018 low. Since January 2022, Nasdaq has dropped 27%. Some believe the tech market is collapsing.
It's bad, but nothing has crashed yet. We're about to get super technical, so buckle up!
I've written a follow-up article about what's next. For a more optimistic view of the crisis' aftermath, see: Tech Diaspora and Silicon Valley crisis
What happened?
Insanity reigned. Last decade, everyone became a unicorn. Seed investments can be made without a product or team. While the "real world" economy suffered from the pandemic for three years, tech companies enjoyed the "new normal."
COVID sped up technology adoption on several fronts, but this "new normal" wasn't so new after many restrictions were lifted. Worse, it lived with disrupted logistics chains, high oil prices, and WW3. The consumer market has felt the industry's boom for almost 3 years. Inflation, unemployment, mental distress...what looked like a fast economic recovery now looks like unfulfilled promises.
People rethink everything they eat. Paying a Netflix subscription instead of buying beef is moronic if you can watch it for free on your cousin’s account. No matter how great your real estate app's UI is, buying a house can wait until mortgage rates drop. PLGProduct Led Growth (PLG) isn't the go-to strategy when consumers have more basic expense priorities.
Exponential growth and investment
Until recently, tech companies believed that non-exponential revenue growth was fatal. Exponential growth entails doing more with less. From Salim Ismail words:
An Exponential Organization (ExO) has 10x the impact of its peers.
Many tech companies' theories are far from reality.
Investors have funded (sometimes non-exponential) growth. Scale-driven companies throw people at problems until they're solved. Need an entire closing team because you’ve just bought a TV prime time add? Sure. Want gold-weight engineers to colorize buttons? Why not?
Tech companies don't need cash flow to do it; they can just show revenue growth and get funding. Even though it's hard to get funding, this was the market's momentum until recently.
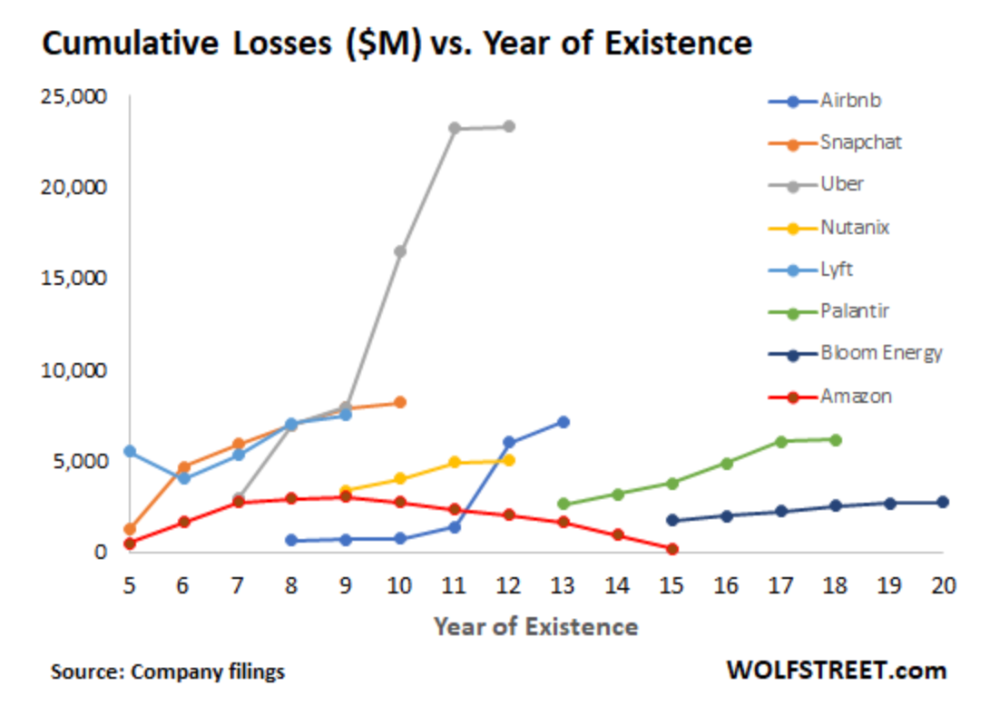
The graph at the beginning of this section shows how industry heavyweights burned money until 2020, despite being far from their market-share seed stage. Being big and being sturdy are different things, and a lot of the tech startups out there are paper tigers. Without investor money, they have no foundation.
A little bit about interest rates
Inflation-driven high interest rates are said to be causing tough times. Investors would rather leave money in the bank than spend it (I myself said it some days ago). It’s not wrong, but it’s also not that simple.
The USA central bank (FED) is a good proxy of global economics. Dollar treasury bonds are the safest investment in the world. Buying U.S. debt, the only country that can print dollars, guarantees payment.
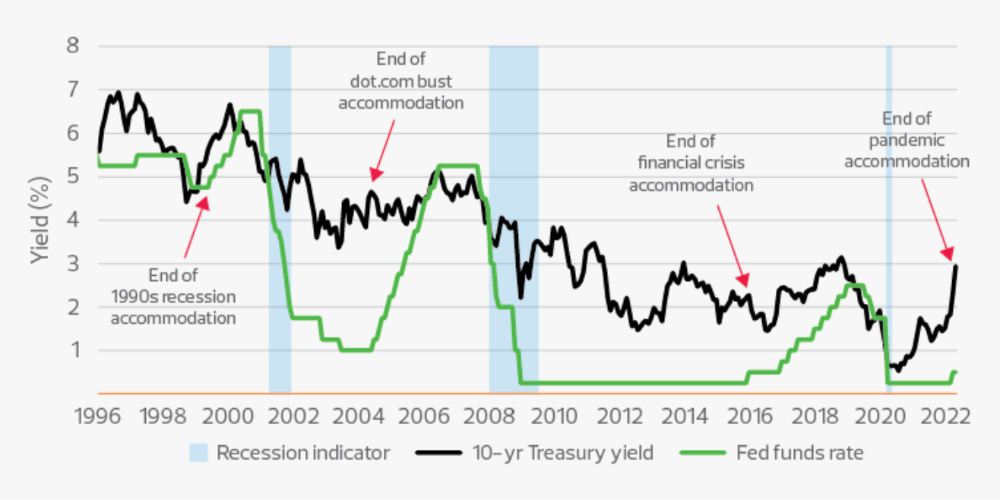
The graph above shows that FED interest rates are low and 10+ year bond yields are near 2018 levels. Nobody was firing at 2018. What’s with that then?
Full explanation is too technical for this article, so I'll just summarize: Bond yields rise due to lack of demand or market expectations of longer-lasting inflation. Safe assets aren't a "easy money" tactic for investors. If that were true, we'd have seen the current scenario before.
Long-term investors are protecting their capital from inflation.
Not a crash, a landing
I bombarded you with info... Let's review:
Consumption is down, hurting revenue.
Tech companies of all ages have been hiring to grow revenue at the expense of profit.
Investors expect inflation to last longer, reducing future investment gains.
Inflation puts pressure on a wheel that was rolling full speed not long ago. Investment spurs hiring, growth, and more investment. Worried investors and consumers reduce the cycle, and hiring follows.
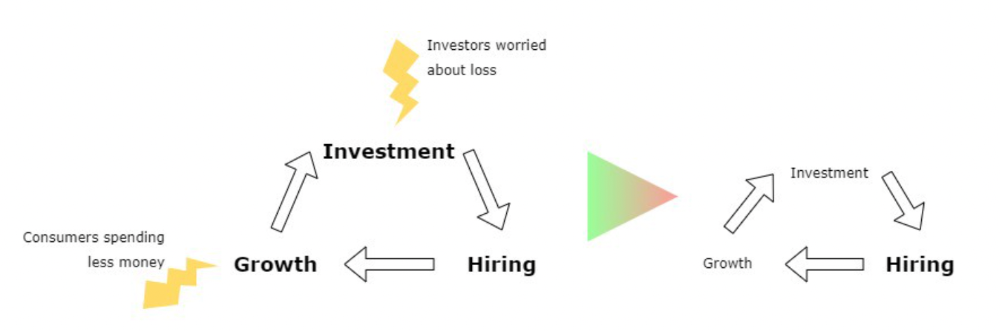
Long-term investors back startups. When the invested company goes public or is sold, it's ok to burn money. What happens when the payoff gets further away? What if all that money sinks? Investors want immediate returns.
Why isn't the market crashing? Technology is not losing capital. It’s expecting change. The market realizes it threw moderation out the window and is reversing course. Profitability is back on the menu.
People solve problems and make money, but they also cost money. Huge cost for the tech industry. Engineers, Product Managers, and Designers earn up to 100% more than similar roles. Businesses must be careful about who they keep and in what positions to avoid wasting money.
What the future holds
From here on, it's all speculation. I found many great articles while researching this piece. Some are cited, others aren't (like this and this). We're in an adjustment period that may or may not last long.
Big companies aren't laying off many workers. Netflix firing 100 people makes headlines, but it's only 1% of their workforce. The biggest seem to prefer not hiring over firing.
Smaller startups beyond the seeding stage may be hardest hit. Without structure or product maturity, many will die.
I expect layoffs to continue for some time, even at Meta or Amazon. I don't see any industry names falling like they did during the .com crisis, but the market will shrink.
If you are currently employed, think twice before moving out and where to.
If you've been fired, hurry, there are still many opportunities.
If you're considering a tech career, wait.
If you're starting a business, I respect you. Good luck.

Bloomberg
3 years ago
Expulsion of ten million Ukrainians
According to recent data from two UN agencies, ten million Ukrainians have been displaced.
The International Organization for Migration (IOM) estimates nearly 6.5 million Ukrainians have relocated. Most have fled the war zones around Kyiv and eastern Ukraine, including Dnipro, Zhaporizhzhia, and Kharkiv. Most IDPs have fled to western and central Ukraine.
Since Russia invaded on Feb. 24, 3.6 million people have crossed the border to seek refuge in neighboring countries, according to the latest UN data. While most refugees have fled to Poland and Romania, many have entered Russia.
Internally displaced figures are IOM estimates as of March 19, based on 2,000 telephone interviews with Ukrainians aged 18 and older conducted between March 9-16. The UNHCR compiled the figures for refugees to neighboring countries on March 21 based on official border crossing data and its own estimates. The UNHCR's top-line total is lower than the country totals because Romania and Moldova totals include people crossing between the two countries.
Sources: IOM, UNHCR
According to IOM estimates based on telephone interviews with a representative sample of internally displaced Ukrainians, over 53% of those displaced are women, and over 60% of displaced households have children.

Victoria Kurichenko
3 years ago
Here's what happened after I launched my second product on Gumroad.
One-hour ebook sales, affiliate relationships, and more.
If you follow me, you may know I started a new ebook in August 2022.
Despite publishing on this platform, my website, and Quora, I'm not a writer.
My writing speed is slow, 2,000 words a day, and I struggle to communicate cohesively.
In April 2022, I wrote a successful guide on How to Write Google-Friendly Blog Posts.
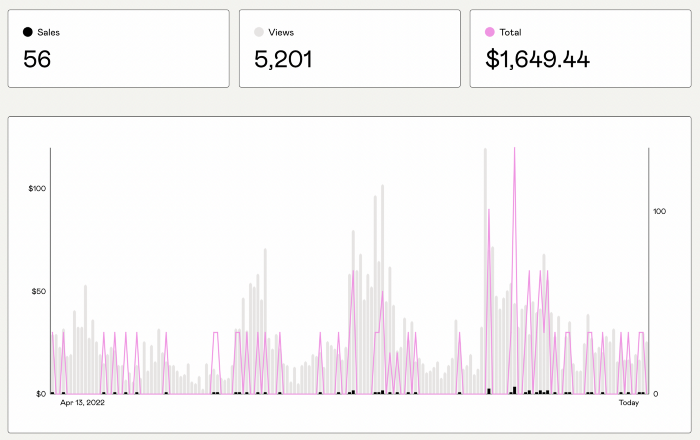
I had no email list or social media presence. I've made $1,600+ selling ebooks.
Evidence:
My first digital offering isn't a book.
It's an actionable guide with my tried-and-true process for writing Google-friendly content.
I'm not bragging.
Established authors like Tim Denning make more from my ebook sales with one newsletter.
This experience taught me writing isn't a privilege.
Writing a book and making money online doesn't require expertise.
Many don't consult experts. They want someone approachable.
Two years passed before I realized my own limits.
I have a brain, two hands, and Internet to spread my message.
I wrote and published a second ebook after the first's success.
On Gumroad, I released my second digital product.
Here's my complete Gumroad evaluation.
Gumroad is a marketplace for content providers to develop and sell sales pages.
Gumroad handles payments and client requests. It's helpful when someone sends a bogus payment receipt requesting an ebook (actual story!).
You'll forget administrative concerns after your first ebook sale.
After my first ebook sale, I did this: I made additional cash!
After every sale, I tell myself, "I built a new semi-passive revenue source."
This thinking shift helps me become less busy while increasing my income and quality of life.
Besides helping others, folks sell evergreen digital things to earn passive money.
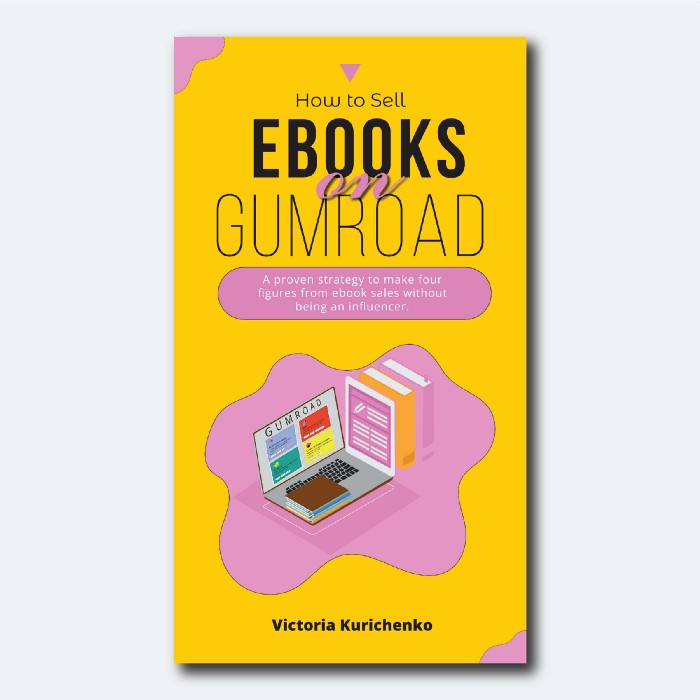
It's in my second ebook.
I explain how I built and sold 50+ copies of my SEO writing ebook without being an influencer.
I show how anyone can sell ebooks on Gumroad and automate their sales process.
This is my ebook.
After publicizing the ebook release, I sold three copies within an hour.
Wow, or meh?
I don’t know.
The answer is different for everyone.
These three sales came from a small email list of 40 motivated fans waiting for my ebook release.
I had bigger plans.
I'll market my ebook on Medium, my website, Quora, and email.
I'm testing affiliate partnerships this time.
One of my ebook buyers is now promoting it for 40% commission.
Become my affiliate if you think your readers would like my ebook.
My ebook is a few days old, but I'm interested to see where it goes.
My SEO writing book started without an email list, affiliates, or 4,000 website visitors. I've made four figures.
I'm slowly expanding my communication avenues to have more impact.
Even a small project can open doors you never knew existed.
So began my writing career.
In summary
If you dare, every concept can become a profitable trip.
Before, I couldn't conceive of creating an ebook.
How to Sell eBooks on Gumroad is my second digital product.
Marketing and writing taught me that anything can be sold online.
