A quick guide to formatting your text on INTΞGRITY
[06/20/2022 update] We have now implemented a powerful text editor, but you can still use markdown.
Markdown:
Headers
SYNTAX:
# This is a heading 1
## This is a heading 2
### This is a heading 3
#### This is a heading 4
RESULT:
This is a heading 1
This is a heading 2
This is a heading 3
This is a heading 4
Emphasis
SYNTAX:
**This text will be bold**
~~Strikethrough~~
*You **can** combine them*
RESULT:
This text will be italic
This text will be bold
You can combine them
Images
SYNTAX:
RESULT:
Videos
SYNTAX:
https://www.youtube.com/watch?v=7KXGZAEWzn0
RESULT:
Links
SYNTAX:
[Int3grity website](https://www.int3grity.com)
RESULT:
Tweets
SYNTAX:
https://twitter.com/samhickmann/status/1503800505864130561
RESULT:
Blockquotes
SYNTAX:
> Human beings face ever more complex and urgent problems, and their effectiveness in dealing with these problems is a matter that is critical to the stability and continued progress of society. \- Doug Engelbart, 1961
RESULT:
Human beings face ever more complex and urgent problems, and their effectiveness in dealing with these problems is a matter that is critical to the stability and continued progress of society. - Doug Engelbart, 1961
Inline code
SYNTAX:
Text inside `backticks` on a line will be formatted like code.
RESULT:
Text inside backticks on a line will be formatted like code.
Code blocks
SYNTAX:
'''js
function fancyAlert(arg) {
if(arg) {
$.facebox({div:'#foo'})
}
}
'''
RESULT:
function fancyAlert(arg) {
if(arg) {
$.facebox({div:'#foo'})
}
}
Maths
We support LaTex to typeset math. We recommend reading the full documentation on the official website
SYNTAX:
$$[x^n+y^n=z^n]$$
RESULT:
[x^n+y^n=z^n]
Tables
SYNTAX:
| header a | header b |
| ---- | ---- |
| row 1 col 1 | row 1 col 2 |
RESULT:
| header a | header b | header c |
|---|---|---|
| row 1 col 1 | row 1 col 2 | row 1 col 3 |
(Edited)
More on Web3 & Crypto

Vitalik
4 years ago
An approximate introduction to how zk-SNARKs are possible (part 2)
If tasked with the problem of coming up with a zk-SNARK protocol, many people would make their way to this point and then get stuck and give up. How can a verifier possibly check every single piece of the computation, without looking at each piece of the computation individually? But it turns out that there is a clever solution.
Polynomials
Polynomials are a special class of algebraic expressions of the form:
- x+5
- x^4
- x^3+3x^2+3x+1
- 628x^{271}+318x^{270}+530x^{269}+…+69x+381
i.e. they are a sum of any (finite!) number of terms of the form cx^k
There are many things that are fascinating about polynomials. But here we are going to zoom in on a particular one: polynomials are a single mathematical object that can contain an unbounded amount of information (think of them as a list of integers and this is obvious). The fourth example above contained 816 digits of tau, and one can easily imagine a polynomial that contains far more.
Furthermore, a single equation between polynomials can represent an unbounded number of equations between numbers. For example, consider the equation A(x)+ B(x) = C(x). If this equation is true, then it's also true that:
- A(0)+B(0)=C(0)
- A(1)+B(1)=C(1)
- A(2)+B(2)=C(2)
- A(3)+B(3)=C(3)
And so on for every possible coordinate. You can even construct polynomials to deliberately represent sets of numbers so you can check many equations all at once. For example, suppose that you wanted to check:
- 12+1=13
- 10+8=18
- 15+8=23
- 15+13=28
You can use a procedure called Lagrange interpolation to construct polynomials A(x) that give (12,10,15,15) as outputs at some specific set of coordinates (eg. (0,1,2,3)), B(x) the outputs (1,8,8,13) on thos same coordinates, and so forth. In fact, here are the polynomials:
- A(x)=-2x^3+\frac{19}{2}x^2-\frac{19}{2}x+12
- B(x)=2x^3-\frac{19}{2}x^2+\frac{29}{2}x+1
- C(x)=5x+13
Checking the equation A(x)+B(x)=C(x) with these polynomials checks all four above equations at the same time.
Comparing a polynomial to itself
You can even check relationships between a large number of adjacent evaluations of the same polynomial using a simple polynomial equation. This is slightly more advanced. Suppose that you want to check that, for a given polynomial F, F(x+2)=F(x)+F(x+1) with the integer range {0,1…89} (so if you also check F(0)=F(1)=1, then F(100) would be the 100th Fibonacci number)
As polynomials, F(x+2)-F(x+1)-F(x) would not be exactly zero, as it could give arbitrary answers outside the range x={0,1…98}. But we can do something clever. In general, there is a rule that if a polynomial P is zero across some set S=\{x_1,x_2…x_n\} then it can be expressed as P(x)=Z(x)*H(x), where Z(x)=(x-x_1)*(x-x_2)*…*(x-x_n) and H(x) is also a polynomial. In other words, any polynomial that equals zero across some set is a (polynomial) multiple of the simplest (lowest-degree) polynomial that equals zero across that same set.
Why is this the case? It is a nice corollary of polynomial long division: the factor theorem. We know that, when dividing P(x) by Z(x), we will get a quotient Q(x) and a remainder R(x) is strictly less than that of Z(x). Since we know that P is zero on all of S, it means that R has to be zero on all of S as well. So we can simply compute R(x) via polynomial interpolation, since it's a polynomial of degree at most n-1 and we know n values (the zeros at S). Interpolating a polynomial with all zeroes gives the zero polynomial, thus R(x)=0 and H(x)=Q(x).
Going back to our example, if we have a polynomial F that encodes Fibonacci numbers (so F(x+2)=F(x)+F(x+1) across x=\{0,1…98\}), then I can convince you that F actually satisfies this condition by proving that the polynomial P(x)=F(x+2)-F(x+1)-F(x) is zero over that range, by giving you the quotient:
H(x)=\frac{F(x+2)-F(x+1)-F(x)}{Z(x)}
Where Z(x) = (x-0)*(x-1)*…*(x-98).
You can calculate Z(x) yourself (ideally you would have it precomputed), check the equation, and if the check passes then F(x) satisfies the condition!
Now, step back and notice what we did here. We converted a 100-step-long computation into a single equation with polynomials. Of course, proving the N'th Fibonacci number is not an especially useful task, especially since Fibonacci numbers have a closed form. But you can use exactly the same basic technique, just with some extra polynomials and some more complicated equations, to encode arbitrary computations with an arbitrarily large number of steps.
see part 3

Onchain Wizard
3 years ago
Three Arrows Capital & Celsius Updates
I read 1k+ page 3AC liquidation documentation so you don't have to. Also sharing revised Celsius recovery plans.
3AC's liquidation documents:
Someone disclosed 3AC liquidation records in the BVI courts recently. I'll discuss the leak's timeline and other highlights.
Three Arrows Capital began trading traditional currencies in emerging markets in 2012. They switched to equities and crypto, then purely crypto in 2018.
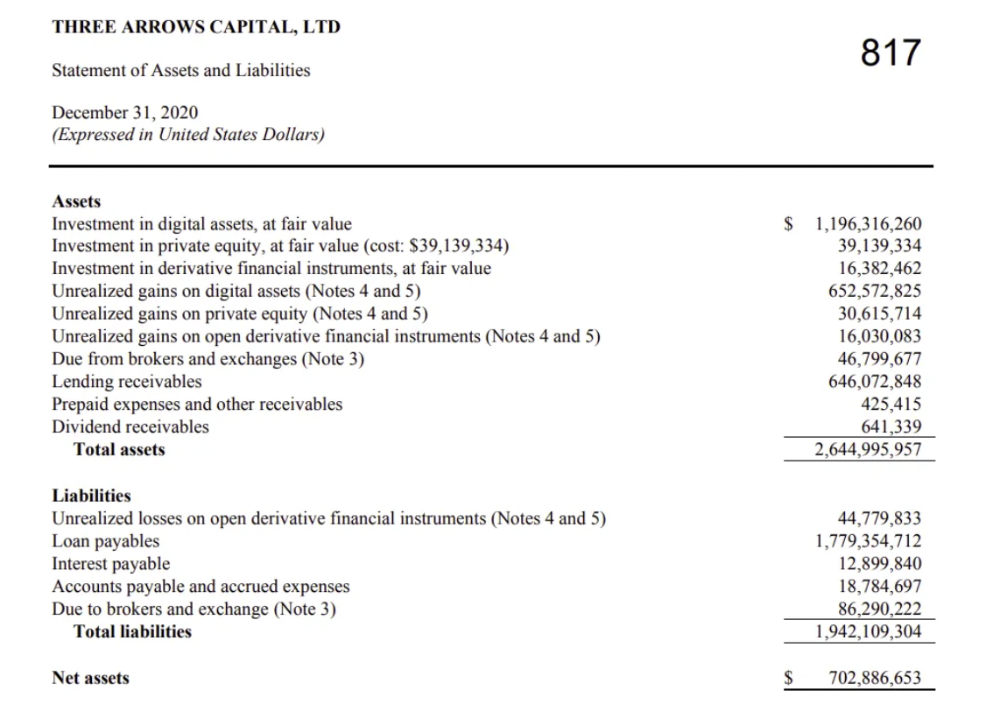
By 2020, the firm had $703mm in net assets and $1.8bn in loans (these guys really like debt).
The firm's net assets under control reached $3bn in April 2022, according to the filings. 3AC had $600mm of LUNA/UST exposure before May 9th 2022, which put them over.
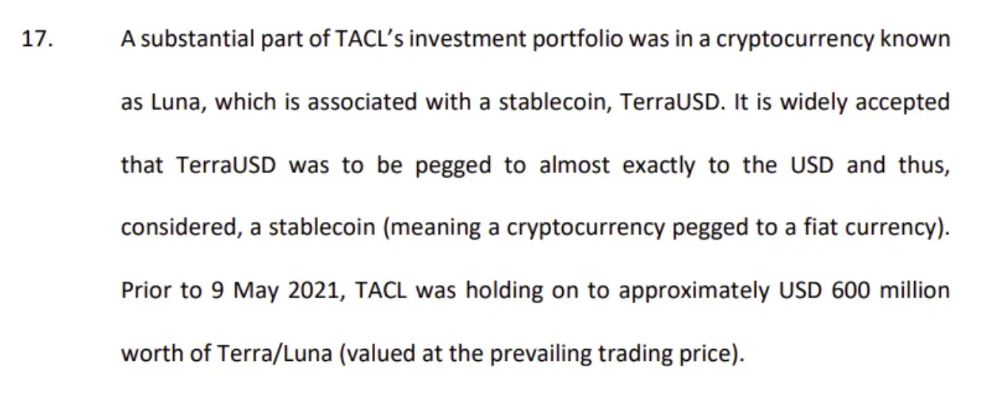
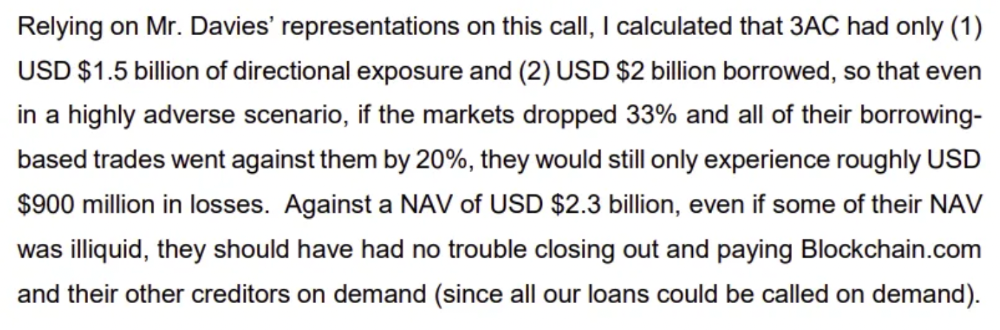
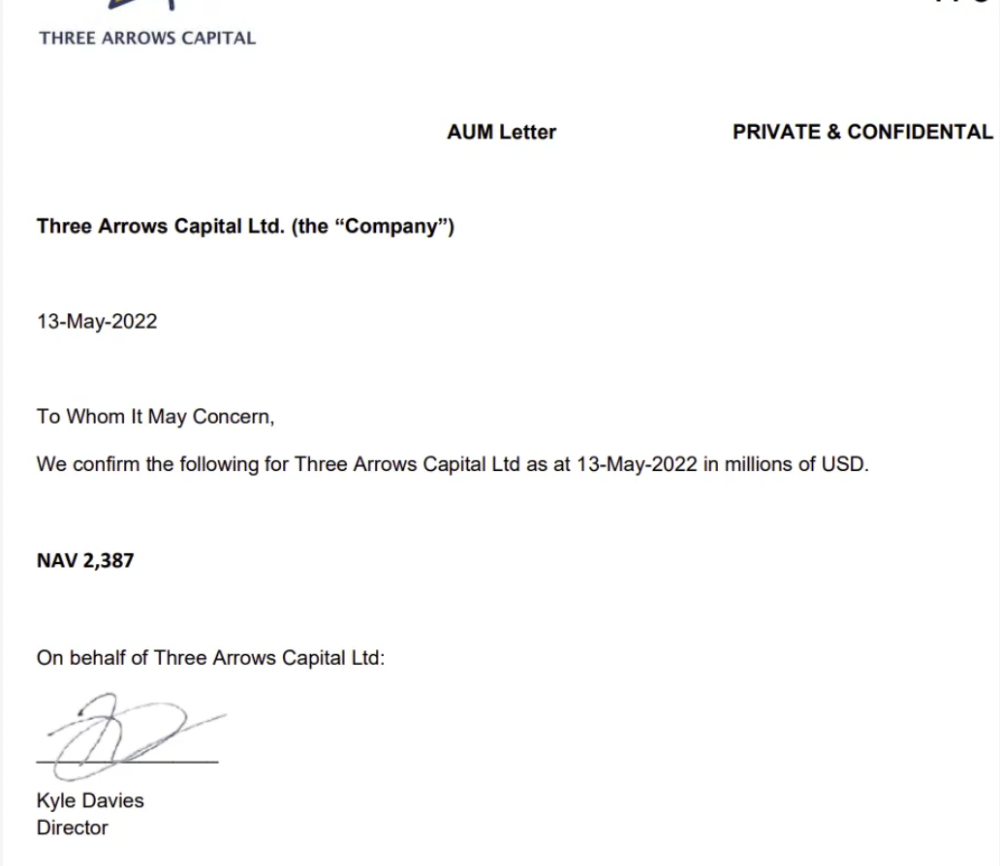
LUNA and UST go to zero quickly (I wrote about the mechanics of the blowup here). Kyle Davies, 3AC co-founder, told Blockchain.com on May 13 that they have $2.4bn in assets and $2.3bn NAV vs. $2bn in borrowings. As BTC and ETH plunged 33% and 50%, the company became insolvent by mid-2022.
3AC sent $32mm to Tai Ping Shen, a Cayman Islands business owned by Su Zhu and Davies' partner, Kelly Kaili Chen (who knows what is going on here).
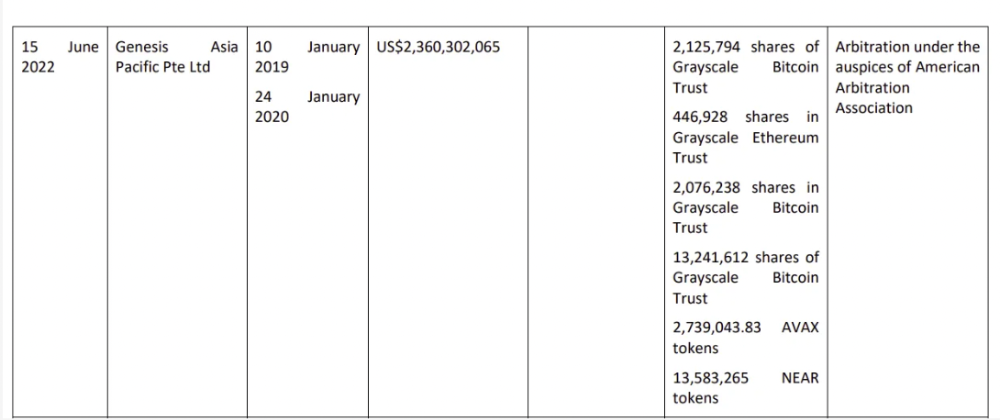
3AC had borrowed over $3.5bn in notional principle, with Genesis ($2.4bn) and Voyager ($650mm) having the most exposure.
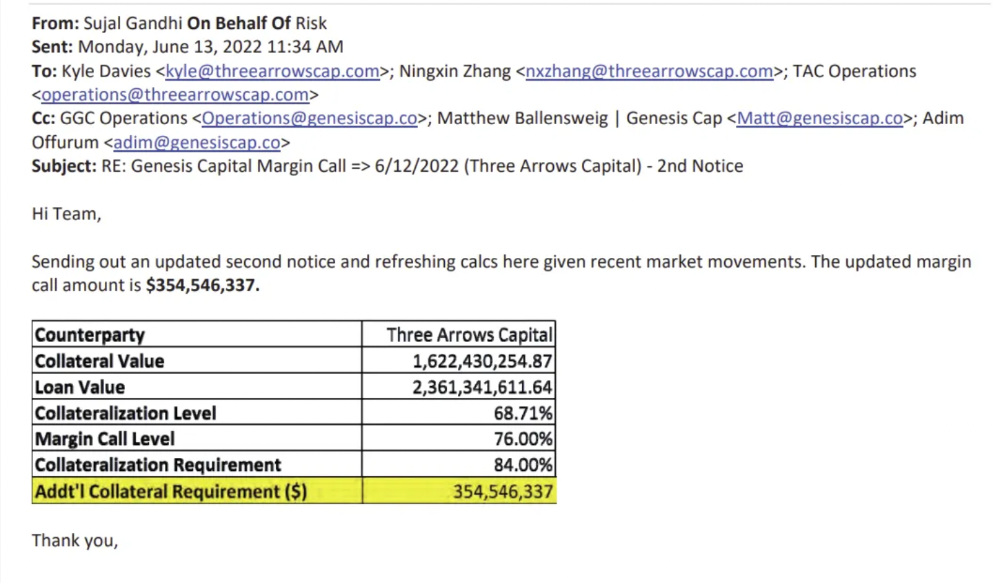
Genesis demanded $355mm in further collateral in June.
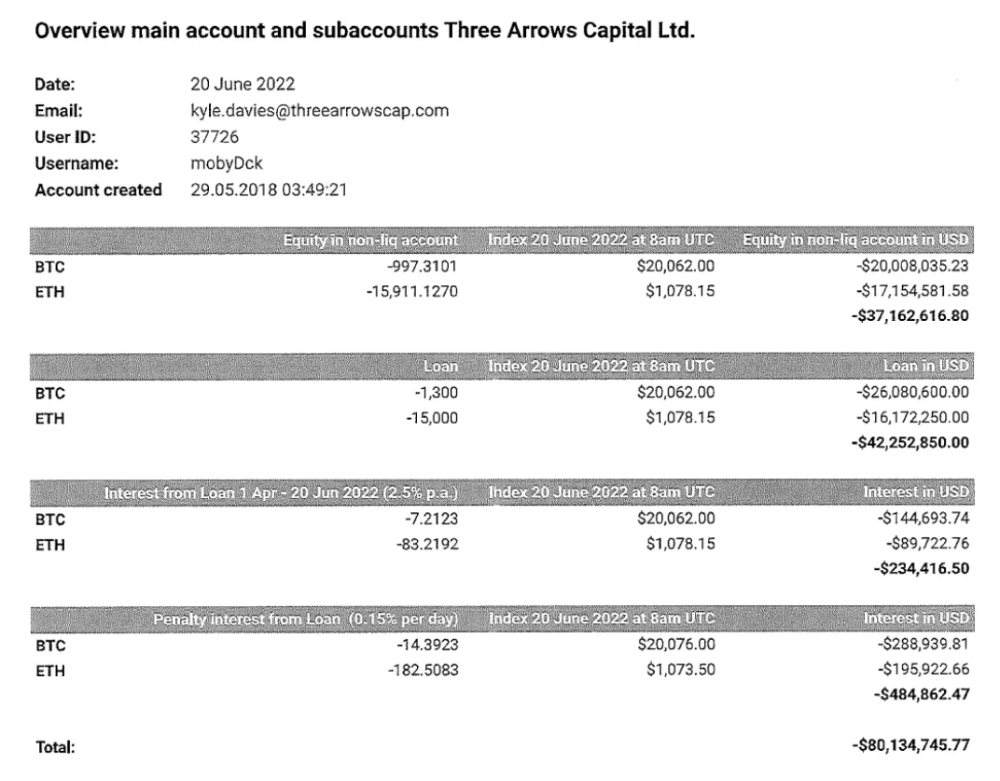
Deribit (another 3AC investment) called for $80 million in mid-June.
Even in mid-June, the corporation was trying to borrow more money to stay afloat. They approached Genesis for another $125mm loan (to pay another lender) and HODLnauts for BTC & ETH loans.
Pretty crazy. 3AC founders used borrowed money to buy a $50 million boat, according to the leak.
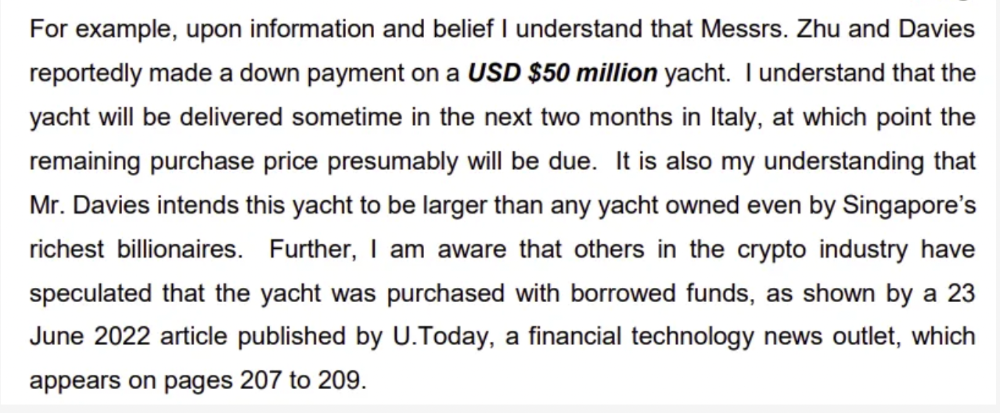
Su requesting for $5m + Chen Kaili Kelly asserting they loaned $65m unsecured to 3AC are identified as creditors.
Celsius:
This bankruptcy presentation shows the Celsius breakdown from March to July 14, 2022. From $22bn to $4bn, crypto assets plummeted from $14.6bn to $1.8bn (ouch). $16.5bn in user liabilities dropped to $4.72bn.
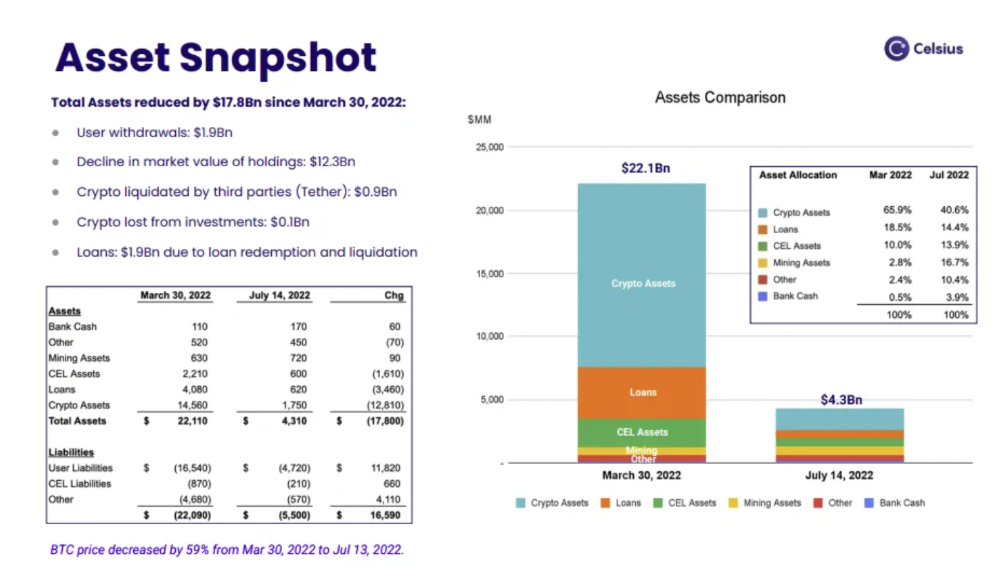
In my recent post, I examined if "forced selling" is over, with Celsius' crypto assets being a major overhang. In this presentation, it looks that Chapter 11 will provide clients the opportunity to accept cash at a discount or remain long crypto. Provided that a fresh source of money is unlikely to enter the Celsius situation, cash at a discount or crypto given to customers will likely remain a near-term market risk - cash at a discount will likely come from selling crypto assets, while customers who receive crypto could sell at any time. I'll share any Celsius updates I find.
Conclusion
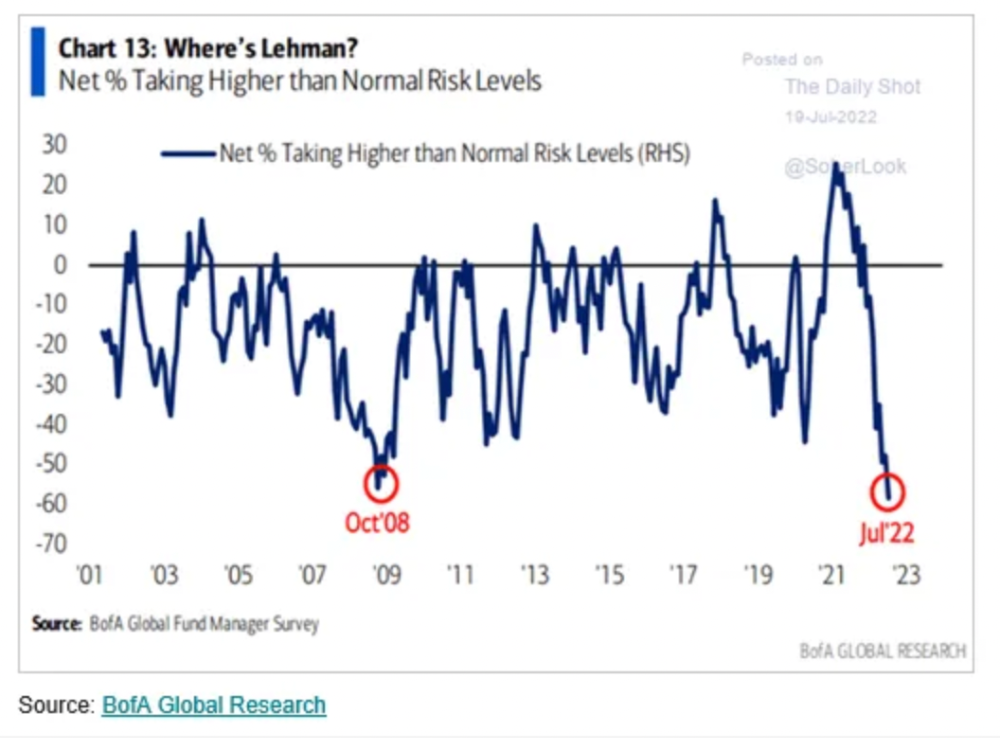
Only Celsius and the Mt Gox BTC unlock remain as forced selling catalysts. While everything went through a "relief" pump, with ETH up 75% from the bottom and numerous alts multiples higher, there are still macro dangers to equities + risk assets. There's a lot of wealth waiting to be deployed in crypto ($153bn in stables), but fund managers are risk apprehensive (lower than 2008 levels).
We're hopefully over crypto's "bottom," with peak anxiety and forced selling behind us, but we may chop around.
To see the full article, click here.

Ryan Weeks
3 years ago
Terra fiasco raises TRON's stablecoin backstop
After Terra's algorithmic stablecoin collapsed in May, TRON announced a plan to increase the capital backing its own stablecoin.
USDD, a near-carbon copy of Terra's UST, arrived on the TRON blockchain on May 5. TRON founder Justin Sun says USDD will be overcollateralized after initially being pegged algorithmically to the US dollar.
A reserve of cryptocurrencies and stablecoins will be kept at 130 percent of total USDD issuance, he said. TRON described the collateral ratio as "guaranteed" and said it would begin publishing real-time updates on June 5.
Currently, the reserve contains 14,040 bitcoin (around $418 million), 140 million USDT, 1.9 billion TRX, and 8.29 billion TRX in a burning contract.
Sun: "We want to hybridize USDD." We have an algorithmic stablecoin and TRON DAO Reserve.
algorithmic failure
USDD was designed to incentivize arbitrageurs to keep its price pegged to the US dollar by trading TRX, TRON's token, and USDD. Like Terra, TRON signaled its intent to establish a bitcoin and cryptocurrency reserve to support USDD in extreme market conditions.
Still, Terra's UST failed despite these safeguards. The stablecoin veered sharply away from its dollar peg in mid-May, bringing down Terra's LUNA and wiping out $40 billion in value in days. In a frantic attempt to restore the peg, billions of dollars in bitcoin were sold and unprecedented volumes of LUNA were issued.
Sun believes USDD, which has a total circulating supply of $667 million, can be backed up.
"Our reserve backing is diversified." Bitcoin and stablecoins are included. USDC will be a small part of Circle's reserve, he said.
TRON's news release lists the reserve's assets as bitcoin, TRX, USDC, USDT, TUSD, and USDJ.
All Bitcoin addresses will be signed so everyone knows they belong to us, Sun said.
Not giving in
Sun told that the crypto industry needs "decentralized" stablecoins that regulators can't touch.
Sun said the Luna Foundation Guard, a Singapore-based non-profit that raised billions in cryptocurrency to buttress UST, mismanaged the situation by trying to sell to panicked investors.
He said, "We must be ahead of the market." We want to stabilize the market and reduce volatility.
Currently, TRON finances most of its reserve directly, but Sun says the company hopes to add external capital soon.
Before its demise, UST holders could park the stablecoin in Terra's lending platform Anchor Protocol to earn 20% interest, which many deemed unsustainable. TRON's JustLend is similar. Sun hopes to raise annual interest rates from 17.67% to "around 30%."
This post is a summary. Read full article here
You might also like

Stephen Moore
3 years ago
A Meta-Reversal: Zuckerberg's $71 Billion Loss
The company's epidemic gains are gone.

Mark Zuckerberg was in line behind Jeff Bezos and Bill Gates less than two years ago. His wealth soared to $142 billion. Facebook's shares reached $382 in September 2021.
What comes next is either the start of something truly innovative or the beginning of an epic rise and fall story.
In order to start over (and avoid Facebook's PR issues), he renamed the firm Meta. Along with the new logo, he announced a turn into unexplored territory, the Metaverse, as the next chapter for the internet after mobile. Or, Zuckerberg believed Facebook's death was near, so he decided to build a bigger, better, cooler ship. Then we saw his vision (read: dystopian nightmare) in a polished demo that showed Zuckerberg in a luxury home and on a spaceship with aliens. Initially, it looked entertaining. A problem was obvious, though. He might claim this was the future and show us using the Metaverse for business, play, and more, but when I took off my headset, I'd realize none of it was genuine.
The stock price is almost as low as January 2019, when Facebook was dealing with the aftermath of the Cambridge Analytica crisis.
Irony surrounded the technology's aim. Zuckerberg says the Metaverse connects people. Despite some potential uses, this is another step away from physical touch with people. Metaverse worlds can cause melancholy, addiction, and mental illness. But forget all the cool stuff you can't afford. (It may be too expensive online, too.)
Metaverse activity slowed for a while. In early February 2022, we got an earnings call update. Not good. Reality Labs lost $10 billion on Oculus and Zuckerberg's Metaverse. Zuckerberg expects losses to rise. Meta's value dropped 20% in 11 minutes after markets closed.
It was a sign of things to come.
The corporation has failed to create interest in Metaverse, and there is evidence the public has lost interest. Meta still relies on Facebook's ad revenue machine, which is also struggling. In July, the company announced a decrease in revenue and missed practically all its forecasts, ending a decade of exceptional growth and relentless revenue. They blamed a dismal advertising demand climate, and Apple's monitoring changes smashed Meta's ad model. Throw in whistleblowers, leaked data revealing the firm knows Instagram negatively affects teens' mental health, the current Capital Hill probe, and the fact TikTok is eating its breakfast, lunch, and dinner, and 2022 might be the corporation's worst year ever.
After a rocky start, tech saw unprecedented growth during the pandemic. It was a tech bubble and then some.
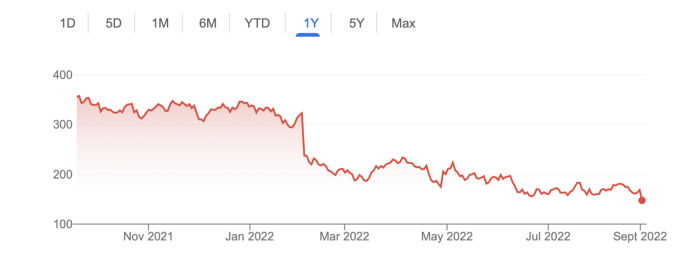
The gains reversed after the dust settled and stock markets adjusted. Meta's year-to-date decline is 60%. Apple Inc is down 14%, Amazon is down 26%, and Alphabet Inc is down 29%. At the time of writing, Facebook's stock price is almost as low as January 2019, when the Cambridge Analytica scandal broke. Zuckerberg owns 350 million Meta shares. This drop costs him $71 billion.
The company's problems are growing, and solutions won't be easy.
Facebook's period of unabated expansion and exorbitant ad revenue is ended, and the company's impact is dwindling as it continues to be the program that only your parents use. Because of the decreased ad spending and stagnant user growth, Zuckerberg will have less time to create his vision for the Metaverse because of the declining stock value and decreasing ad spending.
Instagram is progressively dying in its attempt to resemble TikTok, alienating its user base and further driving users away from Meta-products.
And now that the corporation has shifted its focus to the Metaverse, it is clear that, in its eagerness to improve its image, it fired the launch gun too early. You're fighting a lost battle when you announce an idea and then claim it won't happen for 10-15 years. When the idea is still years away from becoming a reality, the public is already starting to lose interest.
So, as I questioned earlier, is it the beginning of a technological revolution that will take this firm to stratospheric growth and success, or are we witnessing the end of Meta and Zuckerberg himself?

Mia Gradelski
3 years ago
Six Things Best-With-Money People Do Follow

I shouldn't generalize, yet this is true.
Spending is simpler than earning.
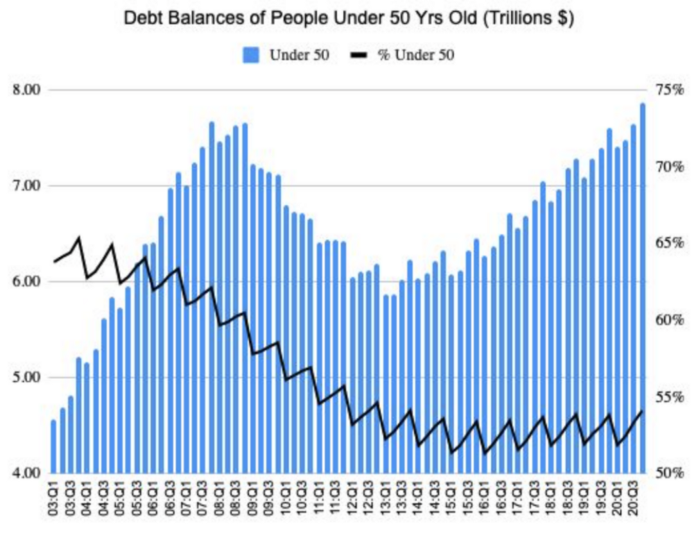
Prove me wrong, but with home debt at $145k in 2020 and individual debt at $67k, people don't have their priorities straight.
Where does this loan originate?
Under-50 Americans owed $7.86 trillion in Q4 20T. That's more than the US's 3-trillion-dollar deficit.
Here’s a breakdown:
🏡 Mortgages/Home Equity Loans = $5.28 trillion (67%)
🎓 Student Loans = $1.20 trillion (15%)
🚗 Auto Loans = $0.80 trillion (10%)
💳 Credit Cards = $0.37 trillion (5%)
🏥 Other/Medical = $0.20 trillion (3%)
Images.google.com
At least the Fed and government can explain themselves with their debt balance which includes:
-Providing stimulus packages 2x for Covid relief
-Stabilizing the economy
-Reducing inflation and unemployment
-Providing for the military, education and farmers
No American should have this much debt.
Don’t get me wrong. Debt isn’t all the same. Yes, it’s a negative number but it carries different purposes which may not be all bad.
Good debt: Use those funds in hopes of them appreciating as an investment in the future
-Student loans
-Business loan
-Mortgage, home equity loan
-Experiences
Paying cash for a home is wasteful. Just if the home is exceptionally uncommon, only 1 in a million on the market, and has an incredible bargain with numerous bidders seeking higher prices should you do so.
To impress the vendor, pay cash so they can sell it quickly. Most people can't afford most properties outright. Only 15% of U.S. homebuyers can afford their home. Zillow reports that only 37% of homes are mortgage-free.
People have clearly overreached.
Ignore appearances.
5% down can buy a 10-bedroom mansion.

Not paying in cash isn't necessarily a negative thing given property prices have increased by 30% since 2008, and throughout the epidemic, we've seen work-from-homers resort to the midwest, avoiding pricey coastal cities like NYC and San Francisco.
By no means do I think NYC is dead, nothing will replace this beautiful city that never sleeps, and now is the perfect time to rent or buy when everything is below average value for people who always wanted to come but never could. Once social distance ends, cities will recover. 24/7 sardine-packed subways prove New York isn't designed for isolation.
When buying a home, pay 20% cash and the balance with a mortgage. A mortgage must be incorporated into other costs such as maintenance, brokerage fees, property taxes, etc. If you're stuck on why a home isn't right for you, read here. A mortgage must be paid until the term date. Whether its a 10 year or 30 year fixed mortgage, depending on interest rates, especially now as the 10-year yield is inching towards 1.25%, it's better to refinance in a lower interest rate environment and pay off your debt as well since the Fed will be inching interest rates up following the 10-year eventually to stabilize the economy, but I believe that won't be until after Covid and when businesses like luxury, air travel, and tourism will get bashed.
Bad debt: I guess the contrary must be true. There is no way to profit from the loan in the future, therefore it is just money down the drain.
-Luxury goods
-Credit card debt
-Fancy junk
-Vacations, weddings, parties, etc.
Credit cards and school loans are the two largest risks to the financial security of those under 50 since banks love to compound interest to affect your credit score and make it tougher to take out more loans, not that you should with that much debt anyhow. With a low credit score and heavy debt, banks take advantage of you because you need aid to pay more for their services. Paying back debt is the challenge for most.
Choose Not Chosen
As a financial literacy advocate and blogger, I prefer not to brag, but I will now. I know what to buy and what to avoid. My parents educated me to live a frugal, minimalist stealth wealth lifestyle by choice, not because we had to.
That's the lesson.
The poorest person who shows off with bling is trying to seem rich.
Rich people know garbage is a bad investment. Investing in education is one of the best long-term investments. With information, you can do anything.
Good with money shun some items out of respect and appreciation for what they have.

Less is more.
Instead of copying the Joneses, use what you have. They may look cheerful and stylish in their 20k ft home, yet they may be as broke as OJ Simpson in his 20-bedroom mansion.
Let's look at what appears good to follow and maintain your wealth.
#1: Quality comes before quantity
Being frugal doesn't entail being cheap and cruel. Rich individuals care about relationships and treating others correctly, not impressing them. You don't have to be rich to be good with money, although most are since they don't live the fantasy lifestyle.
Underspending is appreciating what you have.
Many people believe organic food is the same as washing chemical-laden produce. Hopefully. Organic, vegan, fresh vegetables from upstate may be more expensive in the short term, but they will help you live longer and save you money in the long run.
Consider. You'll save thousands a month eating McDonalds 3x a day instead of fresh seafood, veggies, and organic fruit, but your life will be shortened. If you want to save money and die early, go ahead, but I assume we all want to break the world record for longest person living and would rather spend less. Plus, elderly people get tax breaks, medicare, pensions, 401ks, etc. You're living for free, therefore eating fast food forever is a terrible decision.
With a few longer years, you may make hundreds or millions more in the stock market, spend more time with family, and just live.
Folks, health is wealth.
Consider the future benefit, not simply the cash sign. Cheapness is useless.
Same with stuff. Don't stock your closet with fast-fashion you can't wear for years. Buying inexpensive goods that will fail tomorrow is stupid.
Investing isn't only in stocks. You're living. Consume less.

#2: If you cannot afford it twice, you cannot afford it once
I learned this from my dad in 6th grade. I've been lucky to travel, experience things, go to a great university, and conduct many experiments that others without a stable, decent lifestyle can afford.
I didn't live this way because of my parents' paycheck or financial knowledge.
Saving and choosing caused it.
I always bring cash when I shop. I ditch Apple Pay and credit cards since I can spend all I want on even if my account bounces.
Banks are nasty. When you lose it, they profit.
Cash hinders banks' profits. Carrying a big, hefty wallet with cash is lame and annoying, but it's the best method to only spend what you need. Not for vacation, but for tiny daily expenses.
Physical currency lets you know how much you have for lunch or a taxi.
It's physical, thus losing it prevents debt.
If you can't afford it, it will harm more than help.

#3: You really can purchase happiness with money.
If used correctly, yes.
Happiness and satisfaction differ.
It won't bring you fulfillment because you must work hard on your own to help others, but you can travel and meet individuals you wouldn't otherwise meet.
You can meet your future co-worker or strike a deal while waiting an hour in first class for takeoff, or you can meet renowned people at a networking brunch.
Seen a pattern here?
Your time and money are best spent on connections. Not automobiles or firearms. That’s just stuff. It doesn’t make you a better person.
Be different if you've earned less. Instead of trying to win the lotto or become an NFL star for your first big salary, network online for free.
Be resourceful. Sign up for LinkedIn, post regularly, and leave unengaged posts up because that shows power.
Consistency is beneficial.
I did that for a few months and met amazing people who helped me get jobs. Money doesn't create jobs, it creates opportunities.
Resist social media and scammers that peddle false hopes.
Choose wisely.

#4: Avoid gushing over titles and purchasing trash.
As Insider’s Hillary Hoffower reports, “Showing off wealth is no longer the way to signify having wealth. In the US particularly, the top 1% have been spending less on material goods since 2007.”
I checked my closet. No brand comes to mind. I've never worn a brand's logo and rotate 6 white shirts daily. I have my priorities and don't waste money or effort on clothing that won't fit me in a year.
Unless it's your full-time work, clothing shouldn't be part of our mornings.
Lifestyle of stealth wealth. You're so fulfilled that seeming homeless won't hurt your self-esteem.
That's self-assurance.
Extroverts aren't required.
That's irrelevant.
Showing off won't win you friends.
They'll like your personality.

#5: Time is the most valuable commodity.
Being rich doesn't entail working 24/7 M-F.
They work when they are ready to work.
Waking up at 5 a.m. won't make you a millionaire, but it will inculcate diligence and tenacity in you.
You have a busy day yet want to exercise. You can skip the workout or wake up at 4am instead of 6am to do it.
Emotion-driven lazy bums stay in bed.
Those that are accountable keep their promises because they know breaking one will destroy their week.
Since 7th grade, I've worked out at 5am for myself, not to impress others. It gives me greater energy to contribute to others, especially on weekends and holidays.
It's a habit that I have in my life.
Find something that you take seriously and makes you a better person.
As someone who is close to becoming a millionaire and has encountered them throughout my life, I can share with you a few important differences that have shaped who we are as a society based on the weekends:
-Read
-Sleep
-Best time to work with no distractions
-Eat together
-Take walks and be in nature
-Gratitude
-Major family time
-Plan out weeks
-Go grocery shopping because health = wealth

#6. Perspective is Important
Timing the markets will slow down your career. Professors preach scarcity, not abundance. Why should school teach success? They give us bad advice.
If you trust in abundance and luck by attempting and experimenting, growth will come effortlessly. Passion isn't a term that just appears. Mistakes and fresh people help. You can get money. If you don't think it's worth it, you won't.
You don’t have to be wealthy to be good at money, but most are for these reasons. Rich is a mindset, wealth is power. Prioritize your resources. Invest in yourself, knowing the toughest part is starting.
Thanks for reading!

Techletters
3 years ago
Using Synthesia, DALL-E 2, and Chat GPT-3, create AI news videos
Combining AIs creates realistic AI News Videos.
Powerful AI tools like Chat GPT-3 are trending. Have you combined AIs?
The 1-minute fake news video below is startlingly realistic. Artificial Intelligence developed NASA's Mars exploration breakthrough video (AI). However, integrating the aforementioned AIs generated it.
AI-generated text for the Chat GPT-3 based on a succinct tagline
DALL-E-2 AI generates an image from a brief slogan.
Artificial intelligence-generated avatar and speech
This article shows how to use and mix the three AIs to make a realistic news video. First, watch the video (1 minute).
Talk GPT-3
Chat GPT-3 is an OpenAI NLP model. It can auto-complete text and produce conversational responses.
Try it at the playground. The AI will write a comprehensive text from a brief tagline. Let's see what the AI generates with "Breakthrough in Mars Project" as the headline.
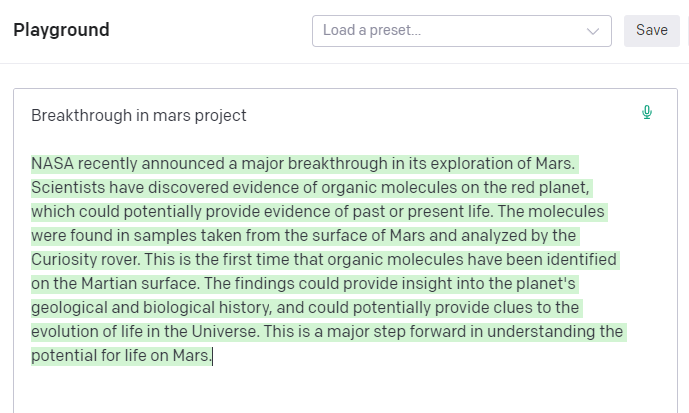
Amazing. Our tagline matches our complete and realistic text. Fake news can start here.
DALL-E-2
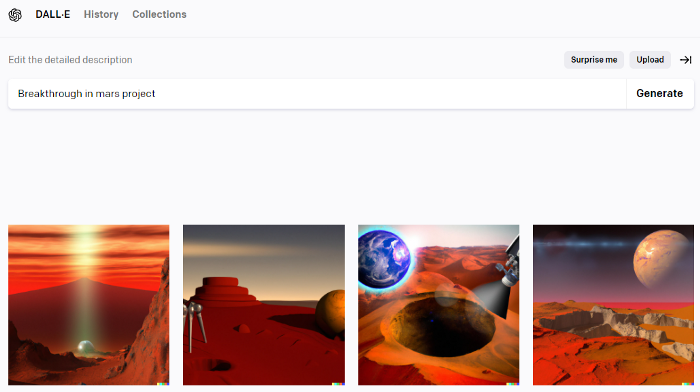
OpenAI's huge transformer-based language model DALL-E-2. Its GPT-3 basis is geared for image generation. It can generate high-quality photos from a brief phrase and create artwork and images of non-existent objects.
DALL-E-2 can create a news video background. We'll use "Breakthrough in Mars project" again. Our AI creates four striking visuals. Last.
Synthesia
Synthesia lets you quickly produce videos with AI avatars and synthetic vocals.
Avatars are first. Rosie it is.
Upload and select DALL-backdrop. E-2's
Copy the Chat GPT-3 content and choose a synthetic voice.
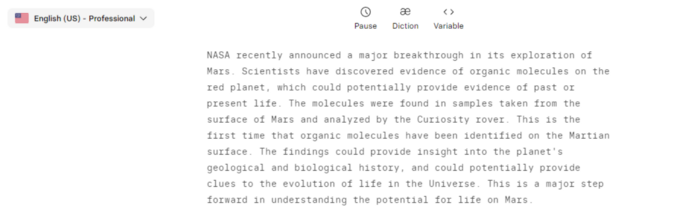
Voice: English (US) Professional.
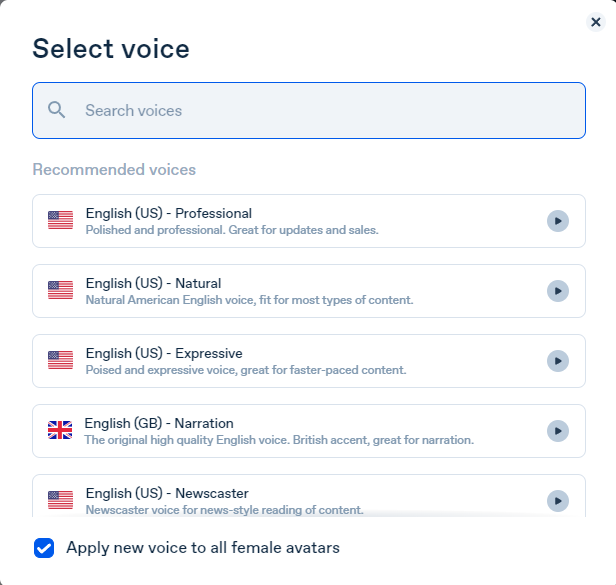
Finally, we generate and watch or download our video.
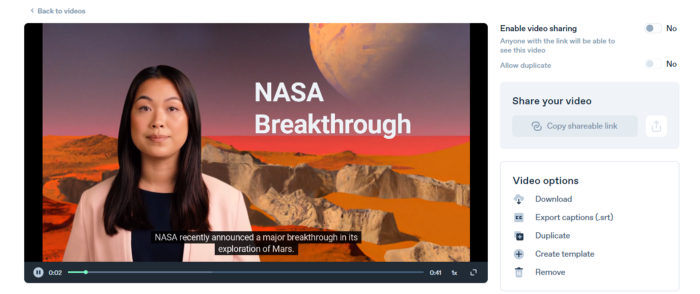
Synthesia AI completes the AI video.
Overview & Resources
We used three AIs to make surprisingly realistic NASA Mars breakthrough fake news in this post. Synthesia generates an avatar and a synthetic voice, therefore it may be four AIs.
These AIs created our fake news.
AI-generated text for the Chat GPT-3 based on a succinct tagline
DALL-E-2 AI generates an image from a brief slogan.
Artificial intelligence-generated avatar and speech