📖 Guide to NFT terms: an NFT glossary.
NFT lingo can be overwhelming. As the NFT market matures and expands so does its own jargon, slang, colloquialisms or acronyms.
This ever-growing NFT glossary goal is to unpack key NFT terms to help you better understand the NFT market or at least not feel like a total n00b in a conversation about NFTs on Reddit, Discord or Twitter.
#
1:1 Art
Art where each piece is one of a kind (1 of 1). Unlike 10K projects, PFP or Generative Art collections have a cap of NFTs released that can range from a few hundreds to 10K.
1/1 of X
Contrary to 1:1 Art, 1/1 of X means each NFT is unique, but part of a large and cohesive collection. E.g: Fidenzas by Tyler Hobbs or Crypto Punks (each Punk is 1/1 of 10,000).
10K Project
A type of NFT collection that consists of approximately 10,000 NFTs (but not strictly).
A
AB
ArtBlocks, the most important platform for generative art currently.
AFAIK
As Far As I Know.
Airdrop
Distribution of an NFT token directly into a crypto wallet for free. Can be used as a marketing campaign or as scam by airdropping fake tokens to empty someone’s wallet.
Alpha
The first or very primitive release of a project. Or Investment term to track how a certain investment outdoes the market. E.g: Alpha of 1.0 = 1% improvement or Alpha of 20.0 = 20% improvement.
Altcoin
Any other crypto that is not Bitcoin. Bitcoin Maximalists can also refer to them as shitcoins.
AMA
Ask Me Anything. NFT creators or artists do sessions where anyone can ask questions about the NFT project, team, vision, etc. Usually hosted on Discord, but also on Reddit or even Youtube.
Ape
Someone can be aping, ape in or aped on an NFT meaning someone is taking a large position relative to its own portfolio size. Some argue that when someone apes can mean that they're following the hype, out of FOMO or without due diligence. Not related directly to the Bored Ape Yatch Club.
ATH
All-Time High. When a NFT project or token reaches the highest price to date.
Avatar project
An NFT collection that consists of avatars that people can use as their profile picture (see PFP) in social media to show they are part of an NFT community like Crypto Punks.
Axie Infinity
ETH blockchain-based game where players battle and trade Axies (digital pets). The main ERC-20 tokens used are Axie Infinity Shards (AXS) and Smooth Love Potions (formerly Small Love Potion) (SLP).
Axie Infinity Shards
AXS is an Eth token that powers the Axie Infinity game.
B
Bag Holder
Someone who holds its position in a crypto or keeps an NFT until it's worthless.
BAYC
Bored Ape Yacht Club. A very successful PFP 1/1 of 10,000 individual ape characters collection. People use BAYC as a Twitter profile picture to brag about being part of this NFT community.
Bearish
Borrowed finance slang meaning someone is doubtful about the current market and that it will crash.
Bear Market
When the Crypto or NFT market is going down in value.
Bitcoin (BTC)
First and original cryptocurrency as outlined in a whitepaper by the anonymous creator(s) Satoshi Nakamoto.
Bitcoin Maximalist
Believer that Bitcoin is the only cryptocurrency needed. All other cryptocurrencies are altcoins or shitcoins.
Blockchain
Distributed, decentralized, immutable database that is the basis of trust in Web 3.0 technology.
Bluechip
When an NFT project has a long track record of success and its value is sustained over time, therefore considered a solid investment.
BTD
Buy The Dip. A bear market can be an opportunity for crypto investors to buy a crypto or NFT at a lower price.
Bullish
Borrowed finance slang meaning someone is optimistic that a market will increase in value aka moon.
Bull market
When the Crypto or NFT market is going up and up in value.
Burn
Common crypto strategy to destroy or delete tokens from the circulation supply intentionally and permanently in order to limit supply and increase the value.
Buying on secondary
Whenever you don’t mint an NFT directly from the project, you can always buy it in secondary NFT marketplaces like OpenSea. Most NFT sales are secondary market sales.
C
Cappin or Capping
Slang for lying or faking. Opposed to no cap which means “no lie”.
Coinbase
Nasdaq listed US cryptocurrency exchange. Coinbase Wallet is one of Coinbase’s products where users can use a Chrome extension or app hot wallet to store crypto and NFTs.
Cold wallet
Otherwise called hardware wallet or cold storage. It’s a physical device to store your cryptocurrencies and/or NFTs offline. They are not connected to the Internet so are at less risk of being compromised.
Collection
A set of NFTs under a common theme as part of a NFT drop or an auction sale in marketplaces like OpenSea or Rarible.
Collectible
A collectible is an NFT that is a part of a wider NFT collection, usually part of a 10k project, PFP project or NFT Game.
Collector
Someone who buys NFTs to build an NFT collection, be part of a NFT community or for speculative purposes to make a profit.
Cope
The opposite of FOMO. When someone doesn’t buy an NFT because one is still dealing with a previous mistake of not FOMOing at a fraction of the price. So choosing to stay out.
Consensus mechanism
Method of authenticating and validating a transaction on a blockchain without the need to trust or rely on a central authority. Examples of consensus mechanisms are Proof of Work (PoW) or Proof of Stake (PoS).
Cozomo de’ Medici
Twitter alias used by Snoop Dogg for crypto and NFT chat.
Creator
An NFT creator is a person that creates the asset for the NFT idea, vision and in many cases the art (e.g. a jpeg, audio file, video file).
Crowsale
Where a crowdsale is the sale of a token that will be used in the business, an Initial Coin Offering (ICO) is the sale of a token that’s linked to the value of the business. Buying an ICO token is akin to buying stock in the company because it entitles you a share of the earnings and profits. Also, some tokens give you voting rights similar to holding stock in the business. The US Securities and Exchange Commission recently ruled that ICOs, but not crowdselling, will be treated as the sale of a security. This basically means that all ICOs must be registered like IPOs and offered only to accredited investors. This dramatically increases the costs and limits the pool of potential buyers.
Crypto Bags/Bags
Refers to how much cryptocurrencies someone holds, as in their bag of coins.
Cryptocurrency
The native coin of a blockchain (or protocol coin), secured by cryptography to be exchanged within a Peer 2 Peer economic system. E.g: Bitcoin (BTC) for the Bitcoin blockchain, Ether (ETH) for the Ethereum blockchain, etc.
Crypto community
The community of a specific crypto or NFT project. NFT communities use Twitter and Discord as their primary social media to hang out.
Crypto exchange
Where someone can buy, sell or trade cryptocurrencies and tokens.
Cryptography
The foundation of blockchain technology. The use of mathematical theory and computer science to encrypt or decrypt information.
CryptoKitties
One of the first and most popular NFT based blockchain games. In 2017, the NFT project almost broke the Ethereum blockchain and increased the gas prices dramatically.
CryptoPunk
Currently one of the most valuable blue chip NFT projects. It was created by Larva Labs. Crypto Punk holders flex their NFT as their profile picture on Twitter.
CT
Crypto Twitter, the crypto-community on Twitter.
Cypherpunks
Movement in the 1980s, advocating for the use of strong cryptography and privacy-enhancing technologies as a route to social and political change. The movement contributed and shaped blockchain tech as we know today.
D
DAO
Stands for Decentralized Autonomous Organization. When a NFT project is structured like a DAO, it grants all the NFT holders voting rights, control over future actions and the NFT’s project direction and vision. Many NFT projects are also organized as DAO to be a community-driven project.
Dapp
Mobile or web based decentralized application that interacts on a blockchain via smart contracts. E.g: Dapp is the frontend and the smart contract is the backend.
DCA
Acronym for Dollar Cost Averaging. An investment strategy to reduce the impact of crypto market volatility. E.g: buying into a crypto asset on a regular monthly basis rather than a big one time purchase.
Ded
Abbreviation for dead like "I sold my Punk for 90 ETH. I am ded."
DeFi
Short for Decentralized Finance. Blockchain alternative for traditional finance, where intermediaries like banks or brokerages are replaced by smart contracts to offer financial services like trading, lending, earning interest, insure, etc.
Degen
Short for degenerate, a gambler who buys into unaudited or unknown NFT or DeFi projects, without proper research hoping to chase high profits.
Delist
No longer offer an NFT for sale on a secondary market like Opensea. NFT Marketplaces can delist an NFT that infringes their rules. Or NFT owners can choose to delist their NFTs (has long as they have sufficient funds for the gas fees) due to price surges to avoid their NFT being bought or sold for a higher price.
Derivative
Projects derived from the original project that reinforces the value and importance of the original NFT. E.g: "alternative" punks.
Dev
A skilled professional who can build NFT projects using smart contracts and blockchain technology.
Dex
Decentralised Exchange that allows for peer-to-peer trustless transactions that don’t rely on a centralized authority to take place. E.g: Uniswap, PancakeSwap, dYdX, Curve Finance, SushiSwap, 1inch, etc.
Diamond Hands
Someone who believes and holds a cryptocurrency or NFT regardless of the crypto or NFT market fluctuations.
Discord
Chat app heavily used by crypto and NFT communities for knowledge sharing and shilling.
DLT
Acronym for Distributed Ledger Technology. It’s a protocol that allows the secure functioning of a decentralized database, through cryptography. This technological infrastructure scraps the need for a central authority to keep in check manipulation or exploitation of the network.
Dog coin
It’s a memecoin based on the Japanese dog breed, Shiba Inu, first popularised by Dogecoin. Other notable coins are Shiba Inu or Floki Inu. These dog coins are frequently subjected to pump and dumps and are extremely volatile. The original dog coin DOGE was created as a joke in 2013. Elon Musk is one of Dogecoin's most famous supporters.
Doxxed/Doxed
When the identity of an NFT team member, dev or creator is public, known or verifiable. In the NFT market, when a NFT team is doxed it’s a usually sign of confidence and transparency for NFT collectors to ensure they will not be scammed for an anonymous creator.
Drop
The release of an NFT (single or collection) into the NFT market.
DYOR
Acronym for Do Your Own Research. A common expression used in the crypto or NFT community to disclaim responsibility for the financial/strategy advice someone is providing the community and to avoid being called out by others in theNFT or crypto community.
E
EIP-1559 EIP
Referring to Ethereum Improvement Proposal 1559, commonly known as the London Fork. It’s an upgrade to the Ethereum protocol code to improve the blockchain security and scalability. The major change consists in shifting from a proof-of-work consensus mechanism (PoW) to a low energy and lower gas fees proof-of-stake system (PoS).
ERC-1155
Stands for Ethereum Request for Comment-1155. A multi-token standard that can represent any number of fungible (ERC-20) and non-fungible tokens (ERC-721).
ERC-20
Ethereum Request for Comment-20 is a standard defining a fungible token like a cryptocurrency.
ERC-721
Ethereum Request for Comment-721 is a standard defining a non-fungible token (NFT).
ETH
Aka Ether, the currency symbol for the native cryptocurrency of the Ethereum blockchain.
ETH2.0
Also known as the London Fork or EIP-1559 EIP. It’s an upgrade to the Ethereum network to improve the network’s security and scalability. The most dramatic change is the shift from the proof-of-work consensus mechanism (PoW) to proof-of-stake system (PoS).
Ether
Or ETH, the native cryptocurrency of the Ethereum blockchain.
Ethereum
Network protocol that allows users to create and run smart contracts over a decentralized network.
F
FCFS
Acronym for First Come First Served. Commonly used strategy in a NFT collection drop when the demand surpasses the supply.
Few
Short for "few understand". Similar to the irony behind the "probably nothing" expression. Like X person bought into a popular NFT, because it understands its long term value.
Fiat Currencies or Money
National government-issued currencies like the US Dollar (USD), Euro (EUR) or Great British Pound (GBP) that are not backed by a commodity like silver or gold. FIAT means an authoritative or arbitrary order like a government decree.
Flex
Slang for showing off. In the crypto community, it’s a Lamborghini or a gold Rolex. In the NFT world, it’s a CryptoPunk or BAYC PFP on Twitter.
Flip
Quickly buying and selling crypto or NFTs to make a profit.
Flippening
Colloquial expression coined in 2017 for when Ethereum’s market capitalisation surpasses Bitcoin’s.
Floor Price
It means the lowest asking price for an NFT collection or subset of a collection on a secondary market like OpenSea.
Floor Sweep
Refers when a NFT collector or investor buys all the lowest listed NFTs on a secondary NFT marketplace.
FOMO
Acronym for Fear Of Missing Out. Buying a crypto or NFT out of fear of missing out on the next big thing.
FOMO-in
Buying a crypto or NFT regardless if it's at the top of the market for FOMO.
Fractionalize
Turning one NFT like a Crypto Punk into X number of fractions ERC-20 tokens that prove ownership of that Punk. This allows for i) collective ownership of an NFT, ii) making an expensive NFT affordable for the common NFT collector and iii) adds more liquidity to a very illiquid NFT market.
FR
Abbreviation for For Real?
Fren
Means Friend and what people in the NFT community call each other in an endearing and positive way.
Foundation
An exclusive, by invitation only, NFT marketplace that specializes in NFT art.
Fungible
Means X can be traded for another X and still hold the same value. E.g: My dollars = your dollars. My 1 ether = your 1 ether. My casino chip = your casino chip. On Ethereum, fungible tokens are defined by the ERC-20 standard.
FUD
Acronym for Fear Uncertainty Doubt. It can be a) when someone spreads negative and sometimes false news to discredit a certain crypto or NFT project. Or b) the overall negative feeling regarding the future of the NFT/Crypto project or market, especially when going through a bear market.
Fudder
Someone who has FUD or engages in FUD about a NFT project.
Fudding your own bags
When an NFT collector or crypto investor speaks negatively about an NFT or crypto project he/she has invested in or has a stake in. Usually negative comments about the team or vision.
G
G
Means Gangster. A term of endearment used amongst the NFT Community.
Gas/Gas fees/Gas prices
The fee charged to complete a transaction in a blockchain. These gas prices vary tremendously between the blockchains, the consensus mechanism used to validate transactions or the number of transactions being made at a specific time.
Gas war
When a lot of NFT collectors (or bots) are trying to mint an NFT at once and therefore resulting in gas price surge.
Generative art
Artwork that is algorithmically created by code with unique traits and rarity.
Genesis drop
It refers to the first NFT drop a creator makes on an NFT auction platform.
GG
Interjection for Good Game.
GM
Interjection for Good Morning.
GMI
Acronym for Going to Make It. Opposite of NGMI (NOT Going to Make It).
GOAT
Acronym for Greatest Of All Time.
GTD
Acronym for Going To Dust. When a token or NFT project turns out to be a bad investment.
GTFO
Get The F*ck Out, as in “gtfo with that fud dude” if someone is talking bull.
GWEI
One billionth of an Ether (ETH) also known as a Shannon / Nanoether / Nano — unit of account used to price Ethereum gas transactions.
H
HEN (Hic Et Nunc)
A popular NFT art marketplace for art built on the Tezos blockchain. Big NFT marketplace for inexpensive NFTs but not a very user-friendly UI/website.
HODL
Misspelling of HOLD coined in an old Reddit post. Synonym with “Hold On for Dear Life” meaning hold your coin or NFT until the end, whether that they’ll moon or dust.
Hot wallet
Wallets connected to the Internet, less secure than cold wallet because they’re more susceptible to hacks.
Hype
Term used to show excitement or anticipation about an upcoming crypto project or NFT.
I
ICO
Acronym for Initial Coin Offering. It’s the crypto equivalent to a stocks’ IPO (Initial Public Offering) but with far less scrutiny or regulation (leading to a lot of scams). ICO’s are a popular way for crypto projects to raise funds.
IDO
Acronym for Initial Dex Offering. To put it simply it means to launch NFTs or tokens via a decentralized liquidity exchange. It’s a common fundraising method used by upcoming crypto or NFT projects. Many consider IDOs a far better fundraising alternative to ICOs.
IDK
Acronym for I Don’t Know.
IDEK
Acronym for I Don’t Even Know.
Imma
Short for I’m going to be.
IRL
Acronym for In Real Life. Refers to the physical world outside of the online/virtual world of crypto, NFTs, gaming or social media.
IPFS
Acronym for Interplanetary File System. A peer-to-peer file storage system using hashes to recall and preserve the integrity of the file, commonly used to store NFTs outside of the blockchain.
It’s Money Laundering
Someone can use this expression to suggest that NFT prices aren’t real and that actually people are using NFTs to launder money, without providing much proof or explanation on how it works.
IYKYK
Stands for If You Know, You Know This. Similar to the expression "few", used when someone buys into a popular crypto or NFT project, slightly because of FOMO but also because it believes in its long term value.
J
JPEG/JPG
File format typically used to encode NFT art. Some people also use Jpeg to mock people buying NFTs as in “All that money for a jpeg”.
K
KMS
Short for Kill MySelf.
L
Larva Labs/ LL
NFT Creators behind the popular NFT projects like Cryptopunks,Meebits or Autoglyphs.
Laser eyes
Bitcoin meme signalling support for BTC and/or it will break the $100k per coin valuation.
LFG
Acronym for Let’s F*cking Go! A common rallying call used in the crypto or NFT community to lead people into buying an NFT or a crypto.
Liquidity
Term that means that a token or NFT has a high volume activity in the crypto/NFT market. It’s easily sold and resold. But usually the NFT market it’s illiquid when compared to the general crypto market, due to the non-fungibility nature of an NFT (there are less buyers for every NFTs out there).
LMFAO
Stands for Laughing My F*cking Ass Off.
Looks Rare
Ironic expression commonly used in the NFT Community. Rarity is a driver of an NFT’s value.
London Hard Fork
Known as EIP-1559, was an Ethereum code upgrade proposal designed to improve the blockchain security and scalability. It’s major change is to shift from PoW to PoS consensus mechanism.
Long run
Means someone is committed to the NFT market or an NFT project in the long term.
M
Maximalist
Typically refers to Bitcoin Maximalists. People who only believe that Bitcoin is the most secure and resilient blockchain. For Maximalists, all other cryptocurrencies are shitcoins therefore a waste of time, development and money.
McDonald's
Common and ironic expression amongst the crypto community. It means that Mcdonald’s is always a valid backup plan or career in the case all cryptocurrencies crash and disappear.
Meatspace
Synonymous with IRL - In Real Life.
Memecoin
Cryptocurrency like Dogecoin that is based on an internet joke or meme.
Metamask
Popular crypto hot wallet platform to store crypto and NFTs.
Metaverse
Term was coined by writer Neal Stephenson in the 1992 dystopian novel “Snow Crash”. It’s an immersive and digital place where people interact via their avatars. Big tech players like Meta (formerly known as Facebook) and other independent players have been designing their own version of a metaverse. NFTs can have utility for users like buying, trading, winning, accessing, experiencing or interacting with things inside a metaverse.
Mfer
Short for “mother fker”.
Miners
Single person or company that mines one or more cryptocurrencies like Bitcoin or Ethereum. Both blockchains need computing power for their Proof of Work consensus mechanism. Miners provide the computing power and receive coins/tokens in return as payment.
Mining
Mining is the process by which new tokens enter in circulation as for example in the Bitcoin blockchain. Also, mining ensures the validity of new transactions happening in a given blockchain that uses the PoW consensus mechanism. Therefore, the ones who mine are rewarded by ensuring the validity of a blockchain.
Mint/Minting
Mint an NFT is the act of publishing your unique instance to a specific blockchain like Ethereum or Tezos blockchain. In simpler terms, a creator is adding a one-of-kind token (NFT) into circulation in a specific blockchain.
Once the NFT is minted - aka created - NFT collectors can i) direct mint, therefore purchase the NFT by paying the specified amount directly into the project’s wallet. Or ii) buy it via an intermediary like an NFT marketplace (e.g: OpenSea, Foundation, Rarible, etc.). Later, the NFT owner can choose to resell the NFT, most NFT creators set up a royalty for every time their NFT is resold.
Minting interval
How often an NFT creator can mint or create tokens.
MOAR
A misspelling that means “more”.
Moon/Mooning
When a coin (e.g. ETH), or token, like an NFT goes exponential in price and the price graph sees a vertical climb. Crypto or NFT users then use the expression that “X token is going to the moon!”.
Moon boys
Slang for crypto or NFT holders who are looking to pump the price dramatically - taking a token to the moon - for short term gains and with no real long term vision or commitment.
N
Never trust, always verify
Treat everyone or every project like something potentially malicious.
New coiner
Crypto slang for someone new to the cryptocurrency space. Usually newcomers can be more susceptible to FUD or scammers.
NFA
Acronym for Not Financial Advice.
NFT
Acronym for Non-Fungible Token. The type of token that can be created, bought, sold, resold and viewed in different dapps. The ERC-721 smart contract standard (Ethereum blockchain) is the most popular amongst NFTs.
NFT Marketplace / NFT Auction platform
Platforms where people can sell and buy NFTs, either via an auction or pay the seller’s price. The largest NFT marketplace is OpenSea. But there are other popular NFT marketplace examples like Foundation, SuperRare, Nifty Gateway, Rarible, Hic et Nunc (HeN), etc.
NFT Whale
A NFT collector or investor who buys a large amount of NFTs.
NGMI
Acronym for Not Going to Make It. For example, something said to someone who has paper hands.
NMP
Acronym for Not My Problem.
Nocoiner
It can be someone who simply doesn’t hold cryptocurrencies, mistrust the crypto market or believes that crypto is either a scam or a ponzi scheme.
Noob/N00b/Newbie
Slang for someone new or not experienced in cryptocurrency or NFTs. These people are more susceptible to scams, drawn into pump and dumps or getting rekt on bad coins.
Normie/Normy
Similar expression for a nocoiner.
NSFW
Acronym for Not Suitable For Work. Referring to online content inappropriate for viewing in public or at work. It began as mostly a tag for sexual content, nudity, or violence, but it has envolved to range a number of other topics that might be delicate or trigger viewers.
Nuclear NFTs
An NFT or collectible with more than 1,000 owners. For the NFT to be sold or resold, every co-owners must give their permission beforehand. Otherwise, the NFT transaction can’t be made.
O
OG
Acronym for Original Gangster and it popularized by 90s Hip Hop culture. It means the first, the original or the person who has been around since the very start and earned respect in the community. In NFT terms, Cryptopunks are the OG of NFTs.
On-chain vs Off-chain
An on-chain NFT is when the artwork (like a jpeg, video or music file) is stored directly into the blockchain making it more secure and less susceptible to being stolen. But, note that most blockchains can only store small amounts of data.
Off-chain NFTs means that the high quality image, music or video file is not stored in the blockchain. But, the NFT data is stored on an external party like a) a centralized server, highly vulnerable to the server being shut down/exploited. Or b) an InterPlanetary File System (IPFS), also an external party but more secure way of finding data because it utilizes a distributed, decentralized system.
OpenSea
By far the largest NFT marketplace in the world, currently.
P
Paper Hands
A crypto or NFT holder who is permeable to negative market sentiment or FUD. And does not hold their crypto or NFT for long. Expression used to describe someone who sells as soon as NFTs enter a bear market.
PFP
Stands for Picture For Profile. Twitter users who hold popular NFTs like Crypto Punk or BAYC use their punk or monkey avatar as their profile picture.
POAP NFT
Stands for Proof of Attendance Protocol. These types of NFTs are awarded to attendees of events, regardless if they’re physical or virtual, as proof you attended.
PoS
Stands for Proof of Stake. A consensus mechanism used by blockchains like Bitcoin or Ethereum to achieve agreement, trust and security in every transaction and keep the integrity of the blockchain intact. PoS mechanisms are considered more environmentally friendly than PoW as they’re lower energy and in emissions.
PoW
Stands for Proof of Work. A consensus mechanism used by blockchains like Bitcoin to achieve agreement, trust and security and keep the transactional integrity of the blockchain intact. PoW mechanism requires a lot of computational power, therefore uses more energy resources and higher CO2 emissions than the PoS mechanism.
Private Key
It can be similar to a password. It’s a secret number that allows users to access their cold or hot wallet funds, prove ownership of a certain address and sign transactions on the blockchain.
It’s not advisable to share a private key with anyone as it makes a person vulnerable to thefts. In case someone loses or forgets its private key, it can use a recovery phrase to restore access to a crypto or NFT wallet.
Pre-mine
A term used in crypto to refer to the act of creating a set amount of tokens before their public launch. It can also be known as a Genesis Sale and is usually associated with Initial Coin Offerings (ICOs) in order to compensate founders, developers or early investors.
Probably nothing
It’s an ironic expression used by NFT enthusiasts to refer to an important or soon to be big news, project or person in the NFT space. Meaning when someone says probably nothing it actually means that it is probably something.
Protocol Coin
Stands for the native coin of a blockchain. As in Ether for the Ethereum blockchain or BTC on the Bitcoin blockchain.
Pump & Dump
The term pump means when a person or a group of people buy or convince others to buy large quantities of a crypto or an NFT with the single goal to drive the price to a peak. When the price peaks, these people sell their position high and for a hefty profit, therefore dumping the price and leaving other slower investors or newbies rekt or at a loss.
R
Rarity
Rarity in NFT terms refers to how rare an NFT is. The rarity can be defined by the number of traits, scarcity or properties of an NFT.
Reaching
Slang for an exaggeration over something to make it sound worse than what it actually is or to take a point/scenario too far.
Recovery phrase
A 12-word phrase that acts like backup for your crypto private keys. A person can recover all of the crypto wallet accounts’ private keys from the recovery phrase. Is not advisable to share the recovery phrase with anyone.
Rekt
Slang for wrecked. When a crypto or NFT project goes wrong or down in value sharply. Or more broadly, when something goes wrong like a person is price out by the gas surge or an NFT floor price goes down.
Right Click Save As
An Ironic expression used by people who don’t understand the value or potential unlocked by NFTs. Person who makes fun that she/he can easily get a digital artwork by Right Click Save As and mock the NFT space and its hype.
Roadmap
The strategy outlined by an NFT project. A way to explain to the NFT community or a potential NFT investor, the different stages, value and the long term vision of the NFT project.
Royalties
NFT creators can set up their NFT so each time their NFT is resold, the creator gets paid a percentage of the sale price.
RN
Acronym for Right Now.
Rug Pull/Rugged
Slang for a scam when the founders, team or developers suddenly leave a crypto project and run away with all the investors’ funds leaving them with nothing.
S
Satoshi Nakamoto
The anonymous creator of the Bitcoin whitepaper and whose identity has never been verified.
Scammer
Someone actively trying to steal other people’s crypto or NFTs.
Secondary
Secondary refers to secondary NFT marketplaces, where NFT collectors or investors can resell NFTs after they’ve been minted. The price of an NFT or NFT collection is determined by those who list them.
Seed phrase
Another name for recovery phrase is the 12-word phrase that allows you to recover all of the crypto wallet accounts’ private keys and regain control of the wallet. Is not advisable to share the seed phrase with anyone.
Seems legit
When an NFT project or a person in the NFT community looks promising and the real deal, meaning seems legitimate. Depending on the context can also be used ironically.
Seems rare
An ironic expression or dismissive comment used by the NFT community. For example, It can be used sarcastically when someone asks for feedback on an NFT they own or created.
Ser
Slang for sir and a polite way of addressing others in an NFT community.
Shill
Expression when someone wants to promote or get exposure to an NFT they own or created.
Shill Thread
It’s a common Twitter strategy to gain traction by encouraging NFT creators to share a link to their NFT project in the hopes of getting bought or noticed by the NFT Community and potential buyers.
Simp/Simping
A NFT holder or creator who comes off as trying to hard impress an NFT whale or investor.
Sh*tposter
A person who mostly posts meme content on Twitter for fun.
SLP
Acronym for Smooth Love Potion. It’s a token players can earn as a reward in the NFT game Axie Infinity.
Smart Contract
A self-executing contract where the terms of the agreement between buyer and seller are directly written into the code and without third party or human intervention. Ethereum is a blockchain that can execute smart contracts, on the contrary to Bitcoin which does not have that capability.
SMFH
Acronym for Shaking My F*cking Head. Common reply to a person showing unbelievable idiocy.
Sock Puppet
Scam account used to lure noob investors into fake investment services.
Snag
It means to buy an NFT quickly and for a very low price. Can also be known as sniping.
Sotheby’s
Very famous auction house that has recently auctioned Beeple’s NFTs or Bored Ape Yacht Club and Crypto Punks’ NFT collections.
Stake
Crypto term for locking up a certain amount of crypto tokens for a set period of time to earn interest. In the NFT space, there are popping up a lot of projects or services that allow NFT holders to earn interest for holding a certain NFT.
Szn
Stands for season referring to crypto or NFT market cycles.
T
TINA
Acronym for There Is No Alternative. Example: someone asks “why are you investing in BTC?”, to which the reply is “TINA”.
TINA RIF
Acronym for There Is No Alternative Resistance Is Futile.
This is the way
A commendation for positive behavior by someone in the NFT Community.
Tokenomics
Referring to the economics of cryptocurrencies, DeFi or NFT projects.
V
Valhalla
Ironic use of the Viking “heaven”. Meaning someone’s NFT collection is either going to be a profitable and blue chip project, therefore they can ascend to Valhalla or is going to tank and that person will have to work at a Mcdonald’s.
Vibe
Term used to express a positive emotional state.
Volatile/Volatility
Term used to describe rapid market fluctuations and crypto or NFT prices go up and down quickly in a short period.
W
WAGMI
Acronym for We Are Going to Make It. Rally cry to build momentum for a crypto or NFT project and lead even more people into buying, shilling or supporting a specific project.
Wallet
There can be a hot or cold wallet, but both are a place where someone can store their cryptocurrency and tokens. Hot wallets are always connected to the Internet like MetaMask, Trust wallet or Phantom. On the contrary cold wallets are hardware wallets to store crypto or NFTs offline like Nano Ledger.
Weak Hands
Synonymous with Paper Hands. Someone who immediately sells their crypto or NFT because of a bear market, FUD or any other negative sentiment.
Web 1.0
Refers to the beginning of the Web. A period from around 1990 to 2005, also known as the read-only web.
Web 2.0
Refers to an iteration of Web 1.0. From 2005 to the present moment, where social media platforms like Facebook, Instagram, TikTok, Google, Twitter, etc reshaped the web, therefore becoming the read-write web.
Web 3.0
A term coined by Ethereum co-founder Gavin Wood and it’s an idea of what the future of the web could look like. Most peoples’ data, info or content would no longer be centralized in Web 2.0 giants - the Big Tech - but decentralized, mostly thanks to blockchain technology. Web 3.0 could be known as read-write-trust web.
Wen
As in When.
Wen Moon
Popular expression from crypto Twitter not so much in the NFT space. Refers to the still distant future when a token will moon.
Whitepaper
Document released by a crypto or NFT project where it lays the technical information behind the concept, vision, roadmap and plans to grow a certain project.
Whale
Someone who owns a large position on a specific or many cryptos or NFTs.
Y
Yodo
Acronym for You Only Die Once. The opposite of Yolo.
Yolo
Acronym for You Only Live Once. A person can use this when they just realized they bought a shitcoin or crap NFT and they’re getting rekt.
Original post
More on NFTs & Art
Scott Duke Kominers
3 years ago
NFT Creators Go Creative Commons Zero (cc0)
On January 1, "Public Domain Day," thousands of creative works immediately join the public domain. The original creator or copyright holder loses exclusive rights to reproduce, adapt, or publish the work, and anybody can use it. It happens with movies, poems, music, artworks, books (where creative rights endure 70 years beyond the author's death), and sometimes source code.
Public domain creative works open the door to new uses. 400,000 sound recordings from before 1923, including Winnie-the-Pooh, were released this year. With most of A.A. Milne's 1926 Winnie-the-Pooh characters now available, we're seeing innovative interpretations Milne likely never planned. The ancient hyphenated version of the honey-loving bear is being adapted for a horror movie: "Winnie-the-Pooh: Blood and Honey"... with Pooh and Piglet as the baddies.
Counterintuitively, experimenting and recombination can occasionally increase IP value. Open source movements allow the public to build on (or fork and duplicate) existing technologies. Permissionless innovation helps Android, Linux, and other open source software projects compete. Crypto's success at attracting public development is also due to its support of open source and "remix culture," notably in NFT forums.
Production memes
NFT projects use several IP strategies to establish brands, communities, and content. Some preserve regular IP protections; others offer NFT owners the opportunity to innovate on connected IP; yet others have removed copyright and other IP safeguards.
By using the "Creative Commons Zero" (cc0) license, artists can intentionally select for "no rights reserved." This option permits anyone to benefit from derivative works without legal repercussions. There's still a lot of confusion between copyrights and NFTs, so nothing here should be considered legal, financial, tax, or investment advice. Check out this post for an overview of copyright vulnerabilities with NFTs and how authors can protect owners' rights. This article focuses on cc0.
Nouns, a 2021 project, popularized cc0 for NFTs. Others followed, including: A Common Place, Anonymice, Blitmap, Chain Runners, Cryptoadz, CryptoTeddies, Goblintown, Gradis, Loot, mfers, Mirakai, Shields, and Terrarium Club are cc0 projects.
Popular crypto artist XCOPY licensed their 1-of-1 NFT artwork "Right-click and Save As Guy" under cc0 in January, exactly one month after selling it. cc0 has spawned many derivatives.
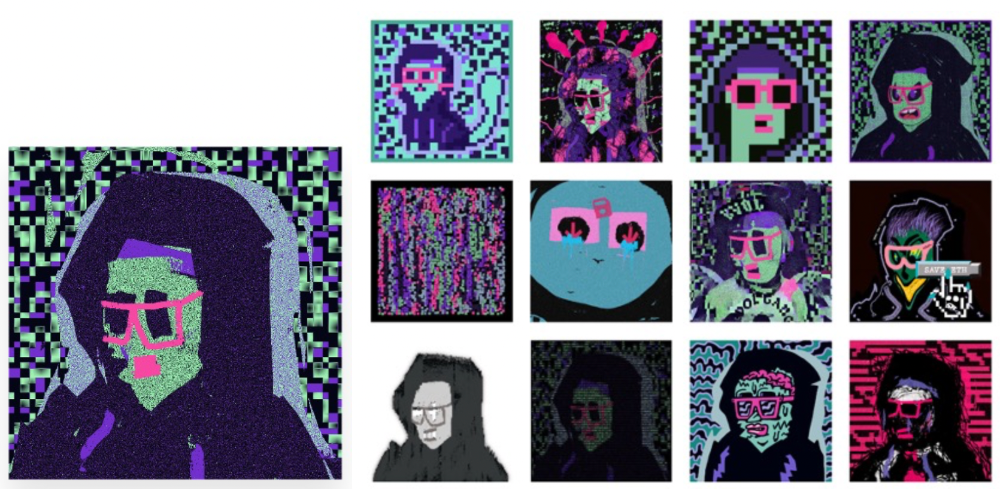
"Right-click Save As Guy" by XCOPY (1)/derivative works (2)
XCOPY said Monday he would apply cc0 to "all his existing art." "We haven't seen a cc0 summer yet, but I think it's approaching," said the artist. - predicting a "DeFi summer" in 2020, when decentralized finance gained popularity.
Why do so many NFT authors choose "no rights"?
Promoting expansions of the original project to create a more lively and active community is one rationale. This makes sense in crypto, where many value open sharing and establishing community.
Creativity depends on cultural significance. NFTs may allow verifiable ownership of any digital asset, regardless of license, but cc0 jumpstarts "meme-ability" by actively, not passively, inviting derivative works. As new derivatives are made and shared, attention might flow back to the original, boosting its reputation. This may inspire new interpretations, leading in a flywheel effect where each derivative adds to the original's worth - similar to platform network effects, where platforms become more valuable as more users join them.
cc0 licence allows creators "seize production memes."
Physical items are also using cc0 NFT assets, thus it's not just a digital phenomenon. The Nouns Vision initiative turned the square-framed spectacles shown on each new NounsDAO NFT ("one per day, forever") into luxury sunglasses. Blitmap's pixel-art has been used on shoes, apparel, and caps. In traditional IP regimes, a single owner controls creation, licensing, and production.
The physical "blitcap" (3rd level) is a descendant of the trait in the cc0 Chain Runners collection (2nd), which uses the "logo" from cc0 Blitmap (1st)! The Logo is Blitmap token #84 and has been used as a trait in various collections. The "Dom Rose" is another popular token. These homages reference Blitmap's influence as a cc0 leader, as one of the earliest NFT projects to proclaim public domain intents. A new collection, Citizens of Tajigen, emerged last week with a Blitcap characteristic.
These derivatives can be a win-win for everyone, not just the original inventors, especially when using NFT assets to establish unique brands. As people learn about the derivative, they may become interested in the original. If you see someone wearing Nouns glasses on the street (or in a Super Bowl ad), you may desire a pair, but you may also be interested in buying an original NounsDAO NFT or related derivative.

Blitmap Logo Hat (1), Chain Runners #780 ft. Hat (2), and Blitmap Original "Logo #87" (3)
Co-creating open source
NFTs' power comes from smart contract technology's intrinsic composability. Many smart contracts can be integrated or stacked to generate richer applications.
"Money Legos" describes how decentralized finance ("DeFi") smart contracts interconnect to generate new financial use cases. Yearn communicates with MakerDAO's stablecoin $DAI and exchange liquidity provider Curve by calling public smart contract methods. NFTs and their underlying smart contracts can operate as the base-layer framework for recombining and interconnecting culture and creativity.
cc0 gives an NFT's enthusiast community authority to develop new value layers whenever, wherever, and however they wish.

Multiple cc0 projects are playable characters in HyperLoot, a Loot Project knockoff.
Open source and Linux's rise are parallels. When the internet was young, Microsoft dominated the OS market with Windows. Linux (and its developer Linus Torvalds) championed a community-first mentality, freely available the source code without restrictions. This led to developers worldwide producing new software for Linux, from web servers to databases. As people (and organizations) created world-class open source software, Linux's value proposition grew, leading to explosive development and industry innovation. According to Truelist, Linux powers 96.3% of the top 1 million web servers and 85% of smartphones.
With cc0 licensing empowering NFT community builders, one might hope for long-term innovation. Combining cc0 with NFTs "turns an antagonistic game into a co-operative one," says NounsDAO cofounder punk4156. It's important on several levels. First, decentralized systems from open source to crypto are about trust and coordination, therefore facilitating cooperation is crucial. Second, the dynamics of this cooperation work well in the context of NFTs because giving people ownership over their digital assets allows them to internalize the results of co-creation through the value that accrues to their assets and contributions, which incentivizes them to participate in co-creation in the first place.
Licensed to create
If cc0 projects are open source "applications" or "platforms," then NFT artwork, metadata, and smart contracts provide the "user interface" and the underlying blockchain (e.g., Ethereum) is the "operating system." For these apps to attain Linux-like potential, more infrastructure services must be established and made available so people may take advantage of cc0's remixing capabilities.
These services are developing. Zora protocol and OpenSea's open source Seaport protocol enable open, permissionless NFT marketplaces. A pixel-art-rendering engine was just published on-chain to the Ethereum blockchain and integrated into OKPC and ICE64. Each application improves blockchain's "out-of-the-box" capabilities, leading to new apps created from the improved building blocks.
Web3 developer growth is at an all-time high, yet it's still a small fraction of active software developers globally. As additional developers enter the field, prospective NFT projects may find more creative and infrastructure Legos for cc0 and beyond.
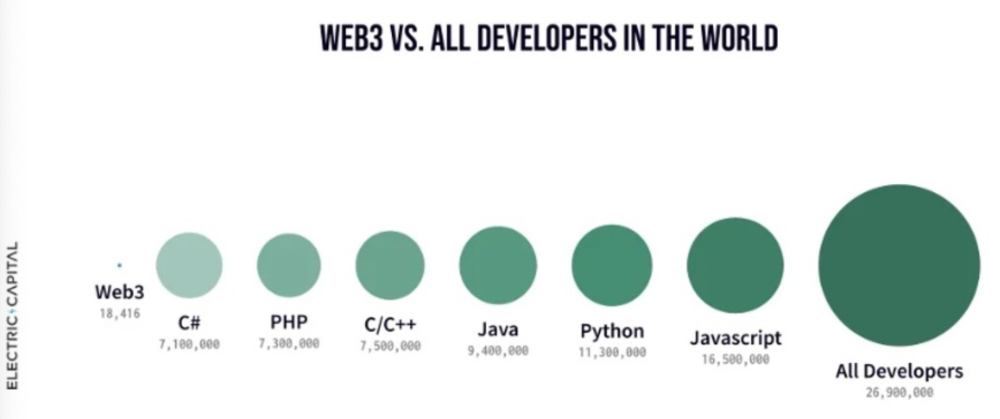
Electric Capital Developer Report (2021), p. 122
Growth requires composability. Users can easily integrate digital assets developed on public standards and compatible infrastructure into other platforms. The Loot Project is one of the first to illustrate decentralized co-creation, worldbuilding, and more in NFTs. This example was low-fi or "incomplete" aesthetically, providing room for imagination and community co-creation.
Loot began with a series of Loot bag NFTs, each listing eight "adventure things" in white writing on a black backdrop (such as Loot Bag #5726's "Katana, Divine Robe, Great Helm, Wool Sash, Divine Slippers, Chain Gloves, Amulet, Gold Ring"). Dom Hofmann's free Loot bags served as a foundation for the community.
Several projects have begun metaphorical (lore) and practical (game development) world-building in a short time, with artists contributing many variations to the collective "Lootverse." They've produced games (Realms & The Crypt), characters (Genesis Project, Hyperloot, Loot Explorers), storytelling initiatives (Banners, OpenQuill), and even infrastructure (The Rift).
Why cc0 and composability? Because consumers own and control Loot bags, they may use them wherever they choose by connecting their crypto wallets. This allows users to participate in multiple derivative projects, such as Genesis Adventurers, whose characters appear in many others — creating a decentralized franchise not owned by any one corporation.
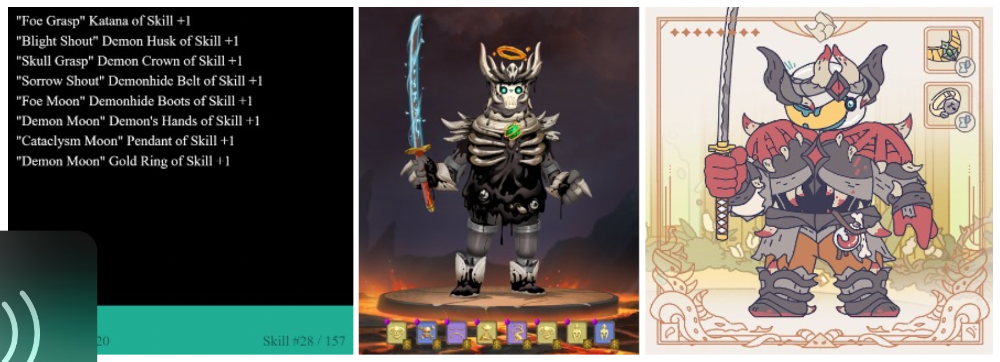
Genesis Project's Genesis Adventurer (1) with HyperLoot (2) and Loot Explorer (3) versions
When to go cc0
There are several IP development strategies NFT projects can use. When it comes to cc0, it’s important to be realistic. The public domain won't make a project a runaway success just by implementing the license. cc0 works well for NFT initiatives that can develop a rich, enlarged ecosystem.
Many of the most successful cc0 projects have introduced flexible intellectual property. The Nouns brand is as obvious for a beer ad as for real glasses; Loot bags are simple primitives that make sense in all adventure settings; and the Goblintown visual style looks good on dwarfs, zombies, and cranky owls as it does on Val Kilmer.
The ideal cc0 NFT project gives builders the opportunity to add value:
vertically, by stacking new content and features directly on top of the original cc0 assets (for instance, as with games built on the Loot ecosystem, among others), and
horizontally, by introducing distinct but related intellectual property that helps propagate the original cc0 project’s brand (as with various Goblintown derivatives, among others).
These actions can assist cc0 NFT business models. Because cc0 NFT projects receive royalties from secondary sales, third-party extensions and derivatives can boost demand for the original assets.
Using cc0 license lowers friction that could hinder brand-reinforcing extensions or lead to them bypassing the original. Robbie Broome recently argued (in the context of his cc0 project A Common Place) that giving away his IP to cc0 avoids bad rehashes down the line. If UrbanOutfitters wanted to put my design on a tee, they could use the actual work instead of hiring a designer. CC0 can turn competition into cooperation.
Community agreement about core assets' value and contribution can help cc0 projects. Cohesion and engagement are key. Using the above examples: Developers can design adventure games around whatever themes and item concepts they desire, but many choose Loot bags because of the Lootverse's community togetherness. Flipmap shared half of its money with the original Blitmap artists in acknowledgment of that project's core role in the community. This can build a healthy culture within a cc0 project ecosystem. Commentator NiftyPins said it was smart to acknowledge the people that constructed their universe. Many OG Blitmap artists have popped into the Flipmap discord to share information.
cc0 isn't a one-size-fits-all answer; NFTs formed around well-established brands may prefer more restrictive licenses to preserve their intellectual property and reinforce exclusivity. cc0 has some superficial similarities to permitting NFT owners to market the IP connected with their NFTs (à la Bored Ape Yacht Club), but there is a significant difference: cc0 holders can't exclude others from utilizing the same IP. This can make it tougher for holders to develop commercial brands on cc0 assets or offer specific rights to partners. Holders can still introduce enlarged intellectual property (such as backstories or derivatives) that they control.
Blockchain technologies and the crypto ethos are decentralized and open-source. This makes it logical for crypto initiatives to build around cc0 content models, which build on the work of the Creative Commons foundation and numerous open source pioneers.
NFT creators that choose cc0 must select how involved they want to be in building the ecosystem. Some cc0 project leaders, like Chain Runners' developers, have kept building on top of the initial cc0 assets, creating an environment derivative projects can plug into. Dom Hofmann stood back from Loot, letting the community lead. (Dom is also working on additional cc0 NFT projects for the company he formed to build Blitmap.) Other authors have chosen out totally, like sartoshi, who announced his exit from the cc0 project he founded, mfers, and from the NFT area by publishing a final edition suitably named "end of sartoshi" and then deactivating his Twitter account. A multi-signature wallet of seven mfers controls the project's smart contract.
cc0 licensing allows a robust community to co-create in ways that benefit all members, regardless of original creators' continuous commitment. We foresee more organized infrastructure and design patterns as NFT matures. Like open source software, value capture frameworks may see innovation. (We could imagine a variant of the "Sleepycat license," which requires commercial software to pay licensing fees when embedding open source components.) As creators progress the space, we expect them to build unique rights and licensing strategies. cc0 allows NFT producers to bootstrap ideas that may take off.

Steffan Morris Hernandez
3 years ago
10 types of cognitive bias to watch out for in UX research & design
10 biases in 10 visuals
Cognitive biases are crucial for UX research, design, and daily life. Our biases distort reality.
After learning about biases at my UX Research bootcamp, I studied Erika Hall's Just Enough Research and used the Nielsen Norman Group's wealth of information. 10 images show my findings.
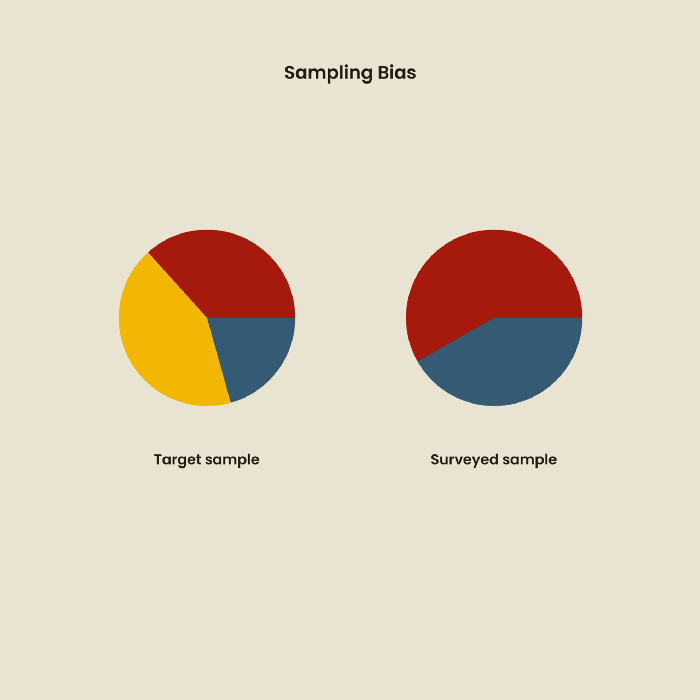
1. Bias in sampling
Misselection of target population members causes sampling bias. For example, you are building an app to help people with food intolerances log their meals and are targeting adult males (years 20-30), adult females (ages 20-30), and teenage males and females (ages 15-19) with food intolerances. However, a sample of only adult males and teenage females is biased and unrepresentative.
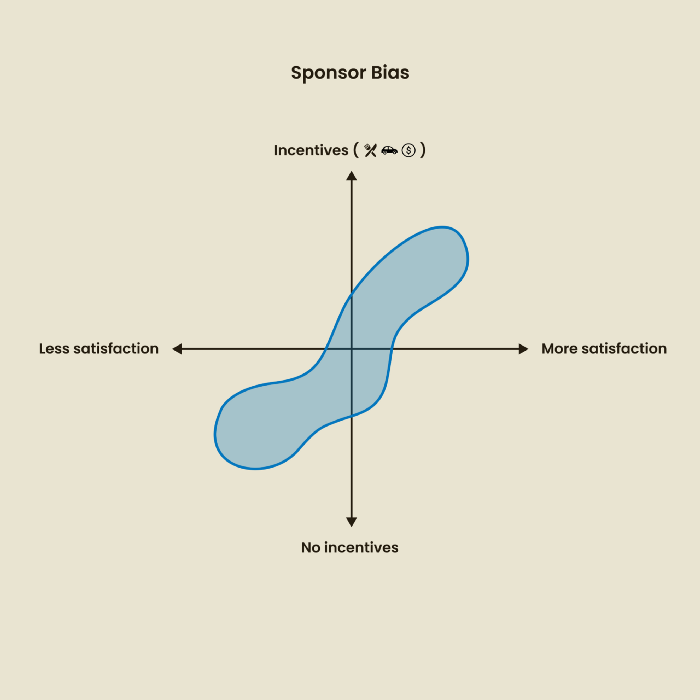
2. Sponsor Disparity
Sponsor bias occurs when a study's findings favor an organization's goals. Beware if X organization promises to drive you to their HQ, compensate you for your time, provide food, beverages, discounts, and warmth. Participants may endeavor to be neutral, but incentives and prizes may bias their evaluations and responses in favor of X organization.
In Just Enough Research, Erika Hall suggests describing the company's aims without naming it.
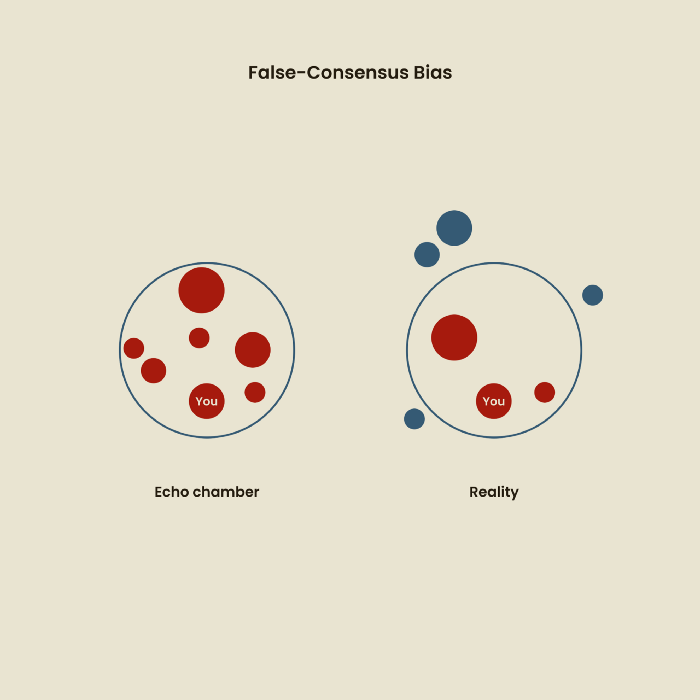
Third, False-Consensus Bias
False-consensus bias is when a person thinks others think and act the same way. For instance, if a start-up designs an app without researching end users' needs, it could fail since end users may have different wants. https://www.nngroup.com/videos/false-consensus-effect/
Working directly with the end user and employing many research methodologies to improve validity helps lessen this prejudice. When analyzing data, triangulation can boost believability.
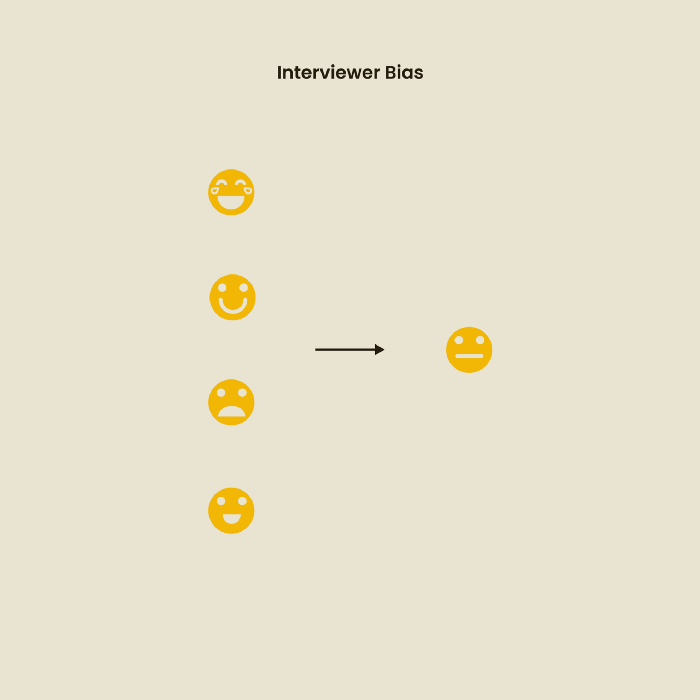
Bias of the interviewer
I struggled with this bias during my UX research bootcamp interviews. Interviewing neutrally takes practice and patience. Avoid leading questions that structure the story since the interviewee must interpret them. Nodding or smiling throughout the interview may subconsciously influence the interviewee's responses.
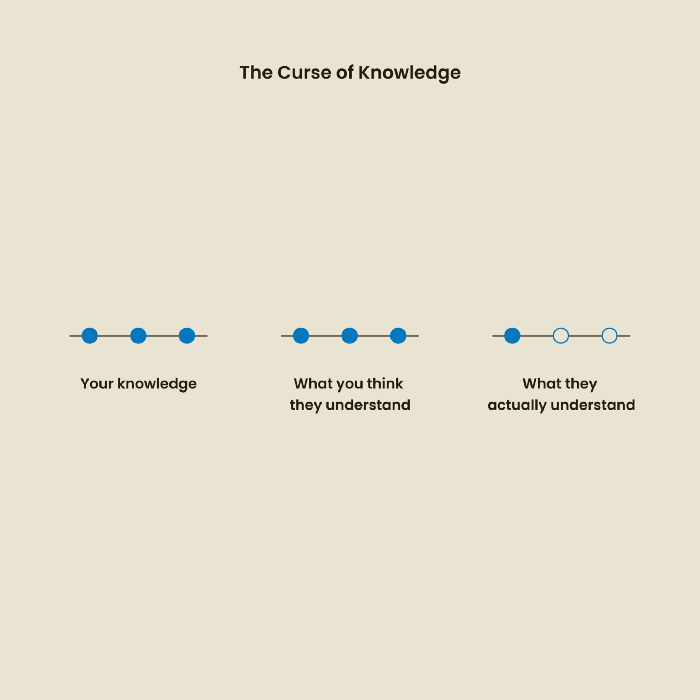
The Curse of Knowledge
The curse of knowledge occurs when someone expects others understand a subject as well as they do. UX research interviews and surveys should reduce this bias because technical language might confuse participants and harm the research. Interviewing participants as though you are new to the topic may help them expand on their replies without being influenced by the researcher's knowledge.
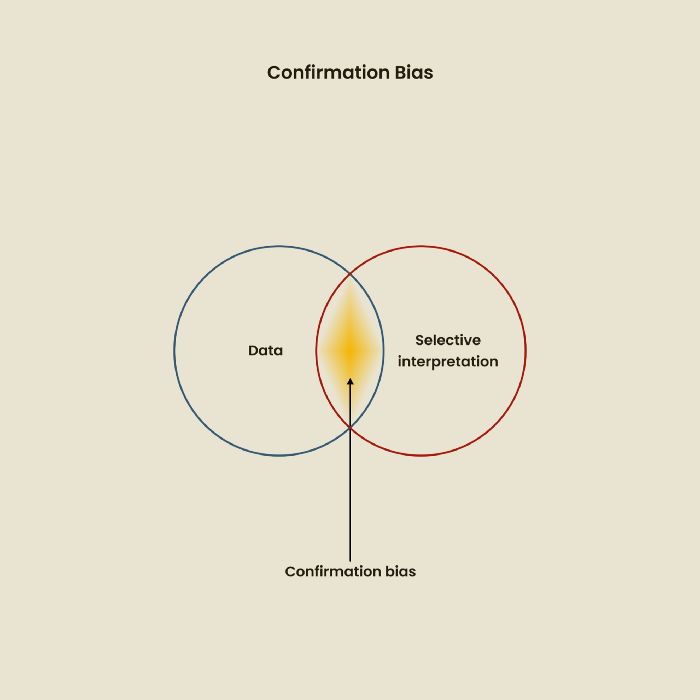
Confirmation Bias
Most prevalent bias. People highlight evidence that supports their ideas and ignore data that doesn't. The echo chamber of social media creates polarization by promoting similar perspectives.
A researcher with confirmation bias may dismiss data that contradicts their research goals. Thus, the research or product may not serve end users.
Design biases
UX Research design bias pertains to study construction and execution. Design bias occurs when data is excluded or magnified based on human aims, assumptions, and preferences.
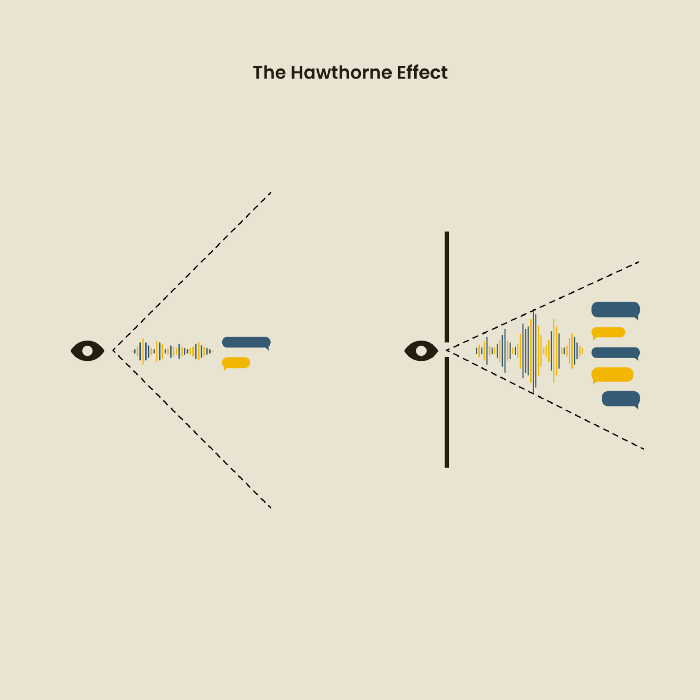
The Hawthorne Impact
Remember when you behaved differently while the teacher wasn't looking? When you behaved differently without your parents watching? A UX research study's Hawthorne Effect occurs when people modify their behavior because you're watching. To escape judgment, participants may act and speak differently.
To avoid this, researchers should blend into the background and urge subjects to act alone.
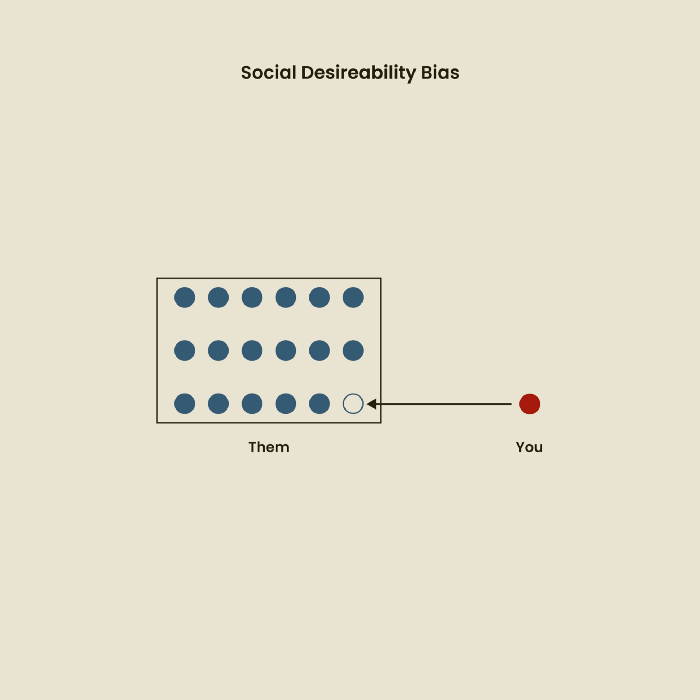
The bias against social desire
People want to belong to escape rejection and hatred. Research interviewees may mislead or slant their answers to avoid embarrassment. Researchers should encourage honesty and confidentiality in studies to address this. Observational research may reduce bias better than interviews because participants behave more organically.
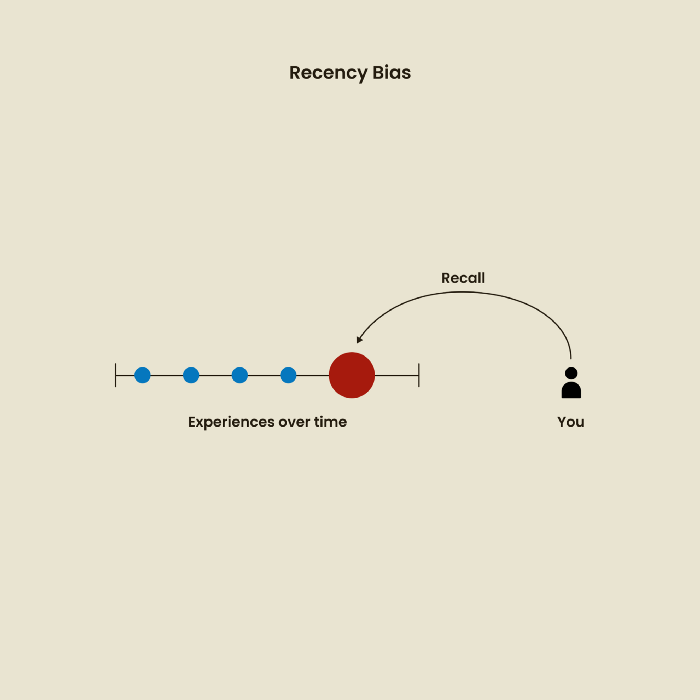
Relative Time Bias
Humans tend to appreciate recent experiences more. Consider school. Say you failed a recent exam but did well in the previous 7 exams. Instead, you may vividly recall the last terrible exam outcome.
If a UX researcher relies their conclusions on the most recent findings instead of all the data and results, recency bias might occur.
I hope you liked learning about UX design, research, and real-world biases.
Yuga Labs
4 years ago
Yuga Labs (BAYC and MAYC) buys CryptoPunks and Meebits and gives them commercial rights
Yuga has acquired the CryptoPunks and Meebits NFT IP from Larva Labs. These include 423 CryptoPunks and 1711 Meebits.
We set out to create in the NFT space because we admired CryptoPunks and the founders' visionary work. A lot of their work influenced how we built BAYC and NFTs. We're proud to lead CryptoPunks and Meebits into the future as part of our broader ecosystem.
"Yuga Labs invented the modern profile picture project and are the best in the world at operating these projects. They are ideal CrytoPunk and Meebit stewards. We are confident that in their hands, these projects will thrive in the emerging decentralized web.”
–The founders of Larva Labs, CryptoPunks, and Meebits
This deal grew out of discussions between our partner Guy Oseary and the Larva Labs founders. One call led to another, and now we're here. This does not mean Matt and John will join Yuga. They'll keep running Larva Labs and creating awesome projects that help shape the future of web3.
Next steps
Here's what we plan to do with CryptoPunks and Meebits now that we own the IP. Owners of CryptoPunks and Meebits will soon receive commercial rights equal to those of BAYC and MAYC holders. Our legal teams are working on new terms and conditions for both collections, which we hope to share with the community soon. We expect a wide range of third-party developers and community creators to incorporate CryptoPunks and Meebits into their web3 projects. We'll build the brand alongside them.
We don't intend to cram these NFT collections into the BAYC club model. We see BAYC as the hub of the Yuga universe, and CryptoPunks as a historical collection. We will work to improve the CryptoPunks and Meebits collections as good stewards. We're not in a hurry. We'll consult the community before deciding what to do next.
For us, NFTs are about culture. We're deeply invested in the BAYC community, and it's inspiring to see them grow, collaborate, and innovate. We're excited to see what CryptoPunks and Meebits do with IP rights. Our goal has always been to create a community-owned brand that goes beyond NFTs, and now we can include CryptoPunks and Meebits.
You might also like

Desiree Peralta
3 years ago
Why Now Is Your Chance To Create A Millionaire Career
People don’t believe in influencers anymore; they need people like you.

Social media influencers have dominated for years. We've seen videos, images, and articles of *famous* individuals unwrapping, reviewing, and endorsing things.
This industry generates billions. This year, marketers spent $2.23 billion on Instagram, $1 million on Youtube, and $775 million on Tiktok. This marketing has helped start certain companies.
Influencers are dying, so ordinary people like us may take over this billion-dollar sector. Why?
Why influencers are perishing
Most influencers lie to their fans, especially on Instagram. Influencers' first purpose was to make their lives so flawless that others would want to buy their stuff.
In 2015, an Australian influencer with 600,000 followers went viral for revealing all her photos and everything she did to seem great before deleting her account.
“I dramatically edited the pictures, I manipulated the environements, and made my life look perfect in social media… I remember I obsessively checked the like count for a full week since uploading it, a selfie that now has close to 2,500 likes. It got 5 likes. This was when I was so hungry for social media validation … This was the reason why I quit social media: for me, personally, it consumed me. I wasn’t living in a 3D world.”
Influencers then lost credibility.
Influencers seem to live in a bubble, separate from us. Thanks to self-popularity love's and constant awareness campaigns, people find these people ridiculous.
Influencers are praised more for showing themselves as natural and common than for showing luxuries and lies.

Little by little, they are dying, making room for a new group to take advantage of this multi-million dollar business, which gives us (ordinary people) a big opportunity to grow on any content creation platform we want.
Why this is your chance to develop on any platform for creating content
In 2021, I wrote “Not everyone who talks about money is a Financial Advisor, be careful of who you take advice from,”. In it, I warned that not everyone with a large following is a reputable source of financial advice.
Other writers hated this post and said I was wrong.
People don't want Jeff Bezos or Elon Musk's counsel, they said. They prefer to hear about their neighbor's restroom problems or his closest friend's terrible business.
Real advice from regular folks.
And I found this was true when I returned to my independent YouTube channel and had more than 1000 followers after having abandoned it with fewer than 30 videos in 2021 since there were already many personal finance and travel channels and I thought mine wasn't special.
People appreciated my videos because I was a 20-something girl trying to make money online, and they believed my advice more than that of influencers with thousands of followers.
I think today is the greatest time to grow on any platform as an ordinary person. Normal individuals give honest recommendations about what works for them and look easier to make because they have the same options as us.
Nobody cares how a millionaire acquired a Lamborghini unless it's entertaining. Education works now. Real counsel from average people is replicable.
Many individuals don't appreciate how false influencers seem (unreal bodies and excessive surgery and retouching) since it makes them feel uneasy.
That's why body-positive advertisements have been so effective, but they've lost ground in places like Tiktok, where the audience wants more content from everyday people than influencers living amazing lives. More people will relate to your content if you appear genuine.
Last thoughts
Influencers are dwindling. People want more real people to give real advice and demonstrate an ordinary life.
People will enjoy anything you tell about your daily life as long as you provide value, and you can build a following rapidly if you're honest.
This is a millionaire industry that is getting more expensive and will go with what works, so stand out immediately.
Isobel Asher Hamilton
3 years ago
$181 million in bitcoin buried in a dump. $11 million to get them back

James Howells lost 8,000 bitcoins. He has $11 million to get them back.
His life altered when he threw out an iPhone-sized hard drive.
Howells, from the city of Newport in southern Wales, had two identical laptop hard drives squirreled away in a drawer in 2013. One was blank; the other had 8,000 bitcoins, currently worth around $181 million.
He wanted to toss out the blank one, but the drive containing the Bitcoin went to the dump.
He's determined to reclaim his 2009 stash.
Howells, 36, wants to arrange a high-tech treasure hunt for bitcoins. He can't enter the landfill.

Newport's city council has rebuffed Howells' requests to dig for his hard drive for almost a decade, stating it would be expensive and environmentally destructive.
I got an early look at his $11 million idea to search 110,000 tons of trash. He expects submitting it to the council would convince it to let him recover the hard disk.
110,000 tons of trash, 1 hard drive
Finding a hard disk among heaps of trash may seem Herculean.
Former IT worker Howells claims it's possible with human sorters, robot dogs, and an AI-powered computer taught to find hard drives on a conveyor belt.
His idea has two versions, depending on how much of the landfill he can search.
His most elaborate solution would take three years and cost $11 million to sort 100,000 metric tons of waste. Scaled-down version costs $6 million and takes 18 months.
He's created a team of eight professionals in AI-powered sorting, landfill excavation, garbage management, and data extraction, including one who recovered Columbia's black box data.
The specialists and their companies would be paid a bonus if they successfully recovered the bitcoin stash.
Howells: "We're trying to commercialize this project."
Howells claimed rubbish would be dug up by machines and sorted near the landfill.
Human pickers and a Max-AI machine would sort it. The machine resembles a scanner on a conveyor belt.
Remi Le Grand of Max-AI told us it will train AI to recognize Howells-like hard drives. A robot arm would select candidates.
Howells has added security charges to his scheme because he fears people would steal the hard drive.
He's budgeted for 24-hour CCTV cameras and two robotic "Spot" canines from Boston Dynamics that would patrol at night and look for his hard drive by day.
Howells said his crew met in May at the Celtic Manor Resort outside Newport for a pitch rehearsal.
Richard Hammond's narrative swings from banal to epic.
Richard Hammond filmed the meeting and created a YouTube documentary on Howells.
Hammond said of Howells' squad, "They're committed and believe in him and the idea."
Hammond: "It goes from banal to gigantic." "If I were in his position, I wouldn't have the strength to answer the door."
Howells said trash would be cleaned and repurposed after excavation. Reburying the rest.
"We won't pollute," he declared. "We aim to make everything better."

After the project is finished, he hopes to develop a solar or wind farm on the dump site. The council is unlikely to accept his vision soon.
A council representative told us, "Mr. Howells can't convince us of anything." "His suggestions constitute a significant ecological danger, which we can't tolerate and are forbidden by our permit."
Will the recovered hard drive work?
The "platter" is a glass or metal disc that holds the hard drive's data. Howells estimates 80% to 90% of the data will be recoverable if the platter isn't damaged.
Phil Bridge, a data-recovery expert who consulted Howells, confirmed these numbers.

If the platter is broken, Bridge adds, data recovery is unlikely.
Bridge says he was intrigued by the proposal. "It's an intriguing case," he added. Helping him get it back and proving everyone incorrect would be a great success story.
Who'd pay?
Swiss and German venture investors Hanspeter Jaberg and Karl Wendeborn told us they would fund the project if Howells received council permission.
Jaberg: "It's a needle in a haystack and a high-risk investment."
Howells said he had no contract with potential backers but had discussed the proposal in Zoom meetings. "Until Newport City Council gives me something in writing, I can't commit," he added.
Suppose he finds the bitcoins.
Howells said he would keep 30% of the data, worth $54 million, if he could retrieve it.
A third would go to the recovery team, 30% to investors, and the remainder to local purposes, including gifting £50 ($61) in bitcoin to each of Newport's 150,000 citizens.
Howells said he opted to spend extra money on "professional firms" to help convince the council.
What if the council doesn't approve?
If Howells can't win the council's support, he'll sue, claiming its actions constitute a "illegal embargo" on the hard drive. "I've avoided that path because I didn't want to cause complications," he stated. I wanted to cooperate with Newport's council.
Howells never met with the council face-to-face. He mentioned he had a 20-minute Zoom meeting in May 2021 but thought his new business strategy would help.
He met with Jessica Morden on June 24. Morden's office confirmed meeting.
After telling the council about his proposal, he can only wait. "I've never been happier," he said. This is our most professional operation, with the best employees.
The "crypto proponent" buys bitcoin every month and sells it for cash.
Howells tries not to think about what he'd do with his part of the money if the hard disk is found functional. "Otherwise, you'll go mad," he added.
This post is a summary. Read the full article here.

Merve Yılmaz
3 years ago
Dopamine detox
This post is for you if you can't read or study for 5 minutes.

If you clicked this post, you may be experiencing problems focusing on tasks. A few minutes of reading may tire you. Easily distracted? Using social media and video games for hours without being sidetracked may impair your dopamine system.
When we achieve a goal, the brain secretes dopamine. It might be as simple as drinking water or as crucial as college admission. Situations vary. Various events require different amounts.
Dopamine is released when we start learning but declines over time. Social media algorithms provide new material continually, making us happy. Social media use slows down the system. We can't continue without an award. We return to social media and dopamine rewards.
Mice were given a button that released dopamine into their brains to study the hormone. The mice lost their hunger, thirst, and libido and kept pressing the button. Think this is like someone who spends all day gaming or on Instagram?
When we cause our brain to release so much dopamine, the brain tries to balance it in 2 ways:
1- Decreases dopamine production
2- Dopamine cannot reach its target.
Too many quick joys aren't enough. We'll want more joys. Drugs and alcohol are similar. Initially, a beer will get you drunk. After a while, 3-4 beers will get you drunk.
Social media is continually changing. Updates to these platforms keep us interested. When social media conditions us, we can't read a book.
Same here. I used to complete a book in a day and work longer without distraction. Now I'm addicted to Instagram. Daily, I spend 2 hours on social media. This must change. My life needs improvement. So I started the 50-day challenge.
I've compiled three dopamine-related methods.
Recommendations:
Day-long dopamine detox
First, take a day off from all your favorite things. Social media, gaming, music, junk food, fast food, smoking, alcohol, friends. Take a break.
Hanging out with friends or listening to music may seem pointless. Our minds are polluted. One day away from our pleasures can refresh us.
2. One-week dopamine detox by selecting
Choose one or more things to avoid. Social media, gaming, music, junk food, fast food, smoking, alcohol, friends. Try a week without Instagram or Twitter. I use this occasionally.
One week all together
One solid detox week. It's the hardest program. First or second options are best for dopamine detox. Time will help you.
You can walk, read, or pray during a dopamine detox. Many options exist. If you want to succeed, you must avoid instant gratification. Success after hard work is priceless.
